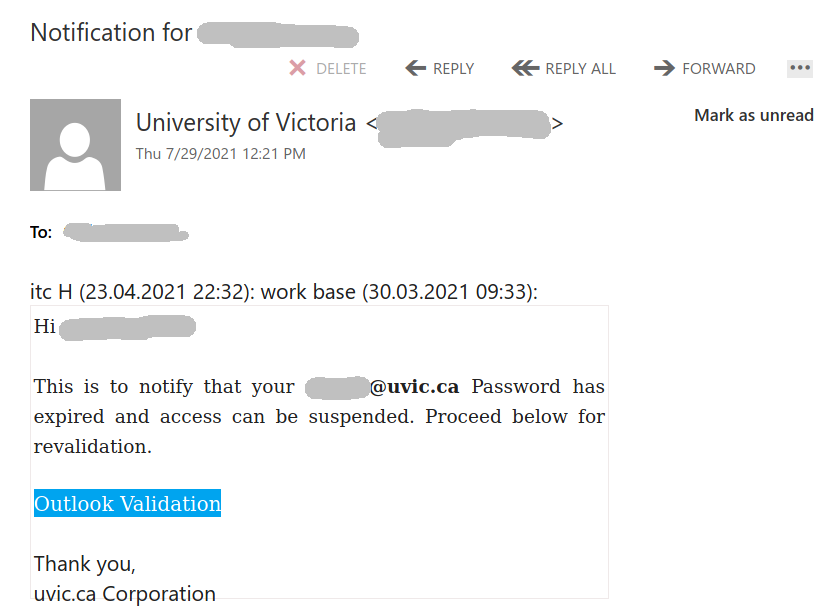
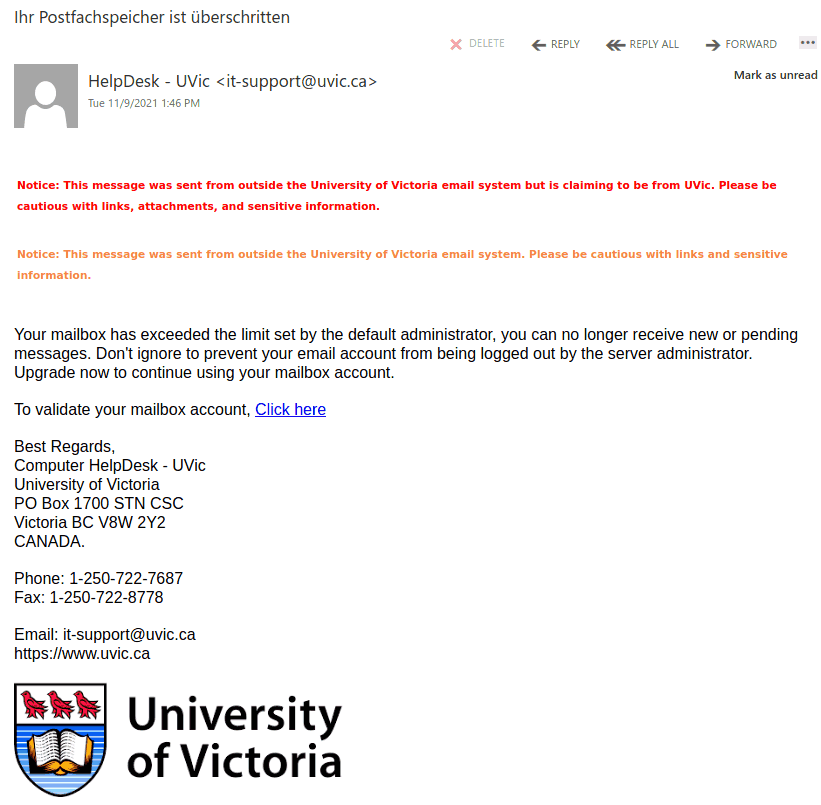
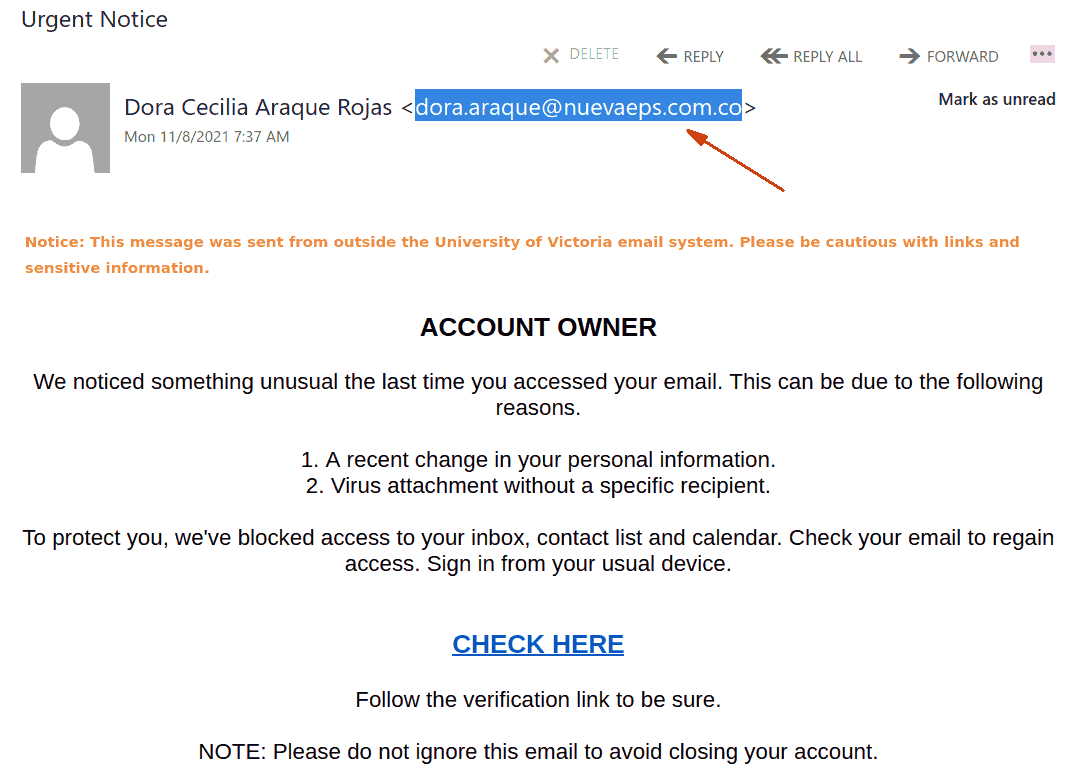
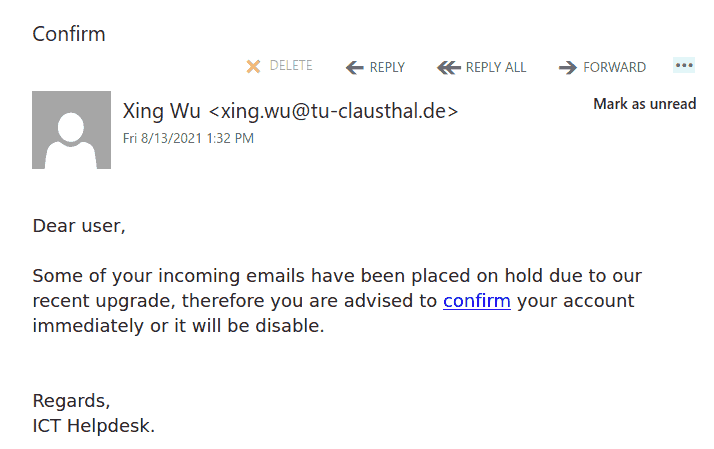
This phish is circulating at UVic today. The malicious actors put some more effort this time. Not only the sender is spoofed to look like a legitimate UVic address but they used the UVic logo and the real address and phone number of the UVic helpdesk.
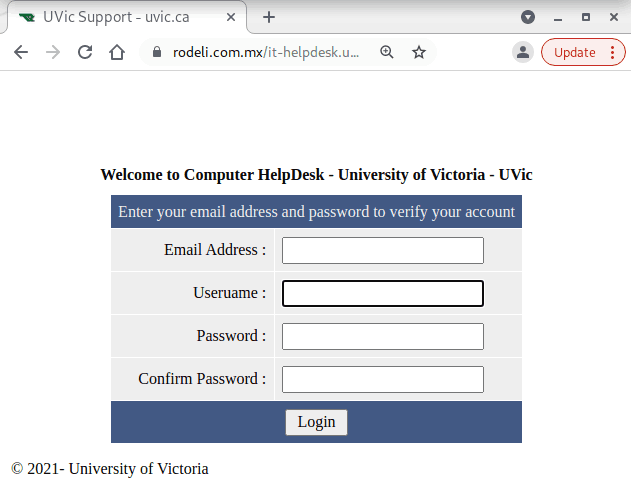
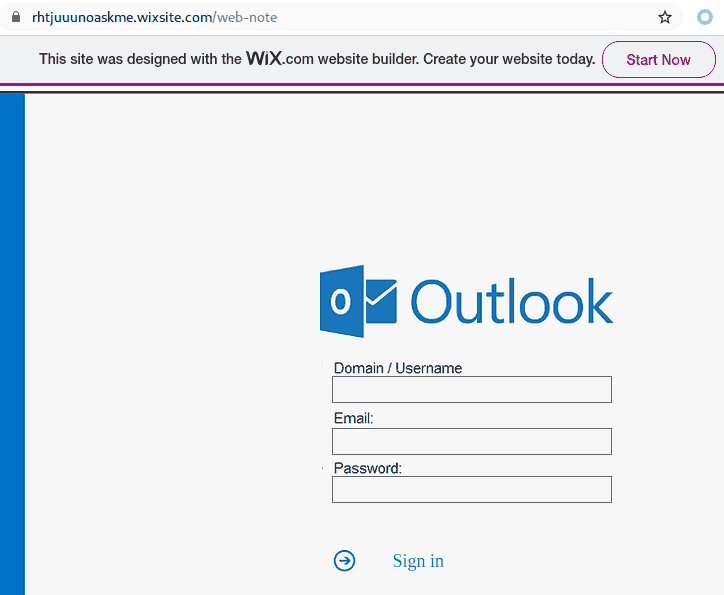
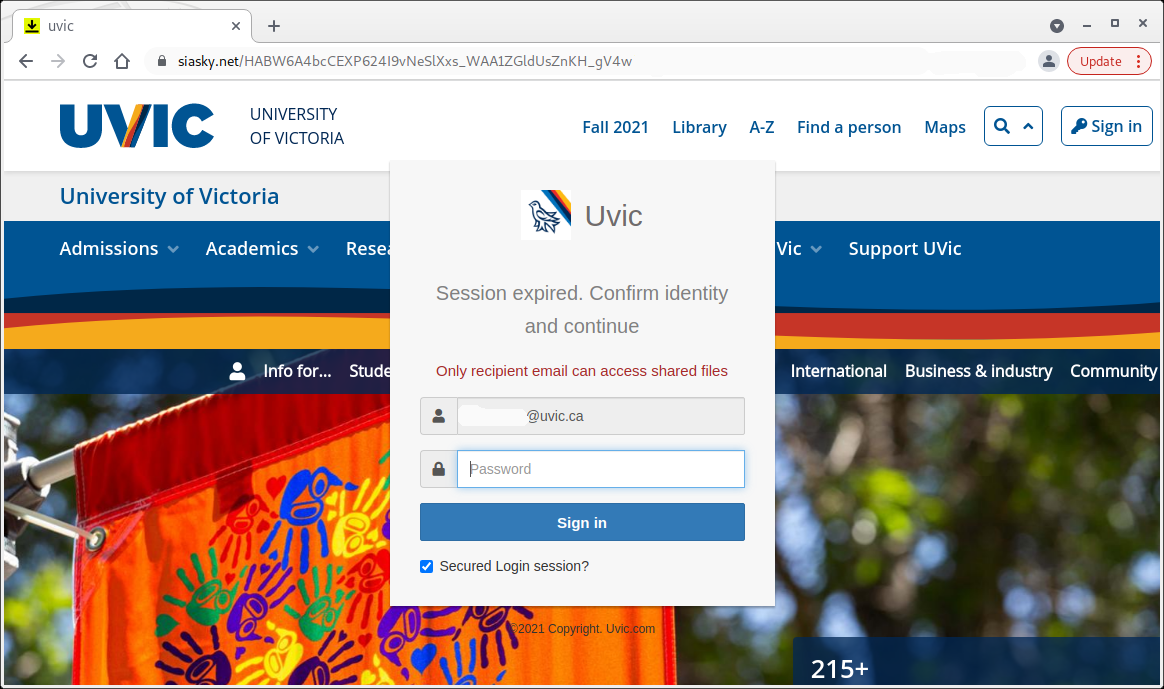
The link points to a webpage in Mexico designed to look as if belonging to UVic.
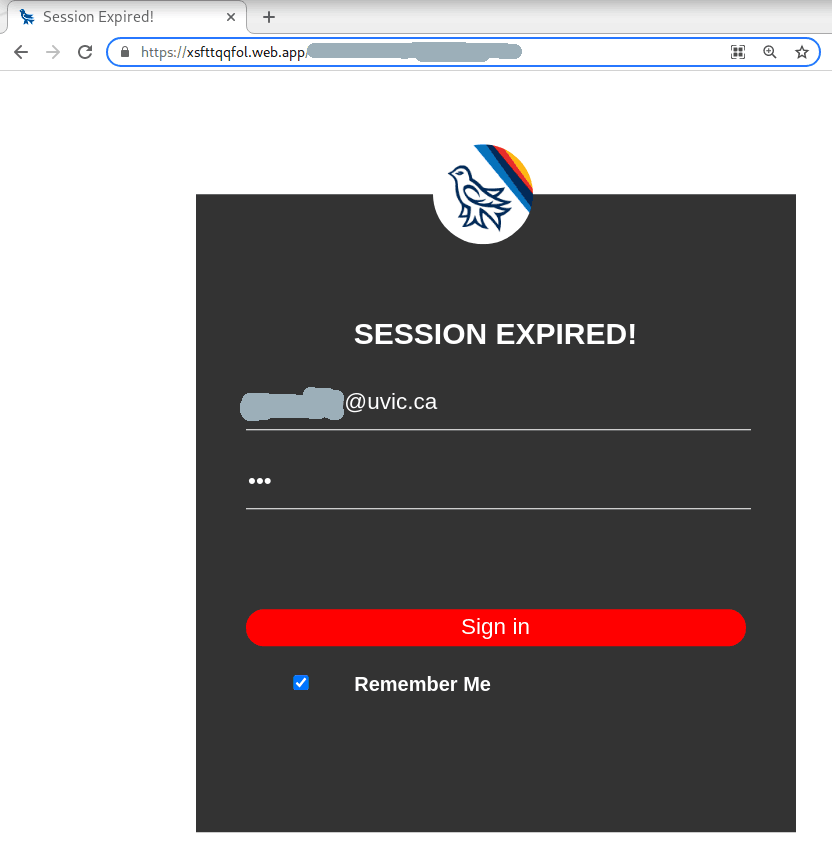
And below is a screenshot of the fake page designed to steal your UVic credentials. As always – we suggest not to be curious and not to click on such links even for a quick look. Some of them may contain malware and infect your machine almost instantly. Our experts open those in dedicated isolated environments.


 —————————————————————————————————–
—————————————————————————————————–