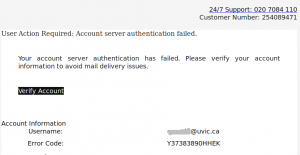
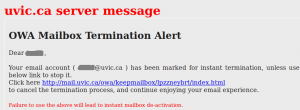
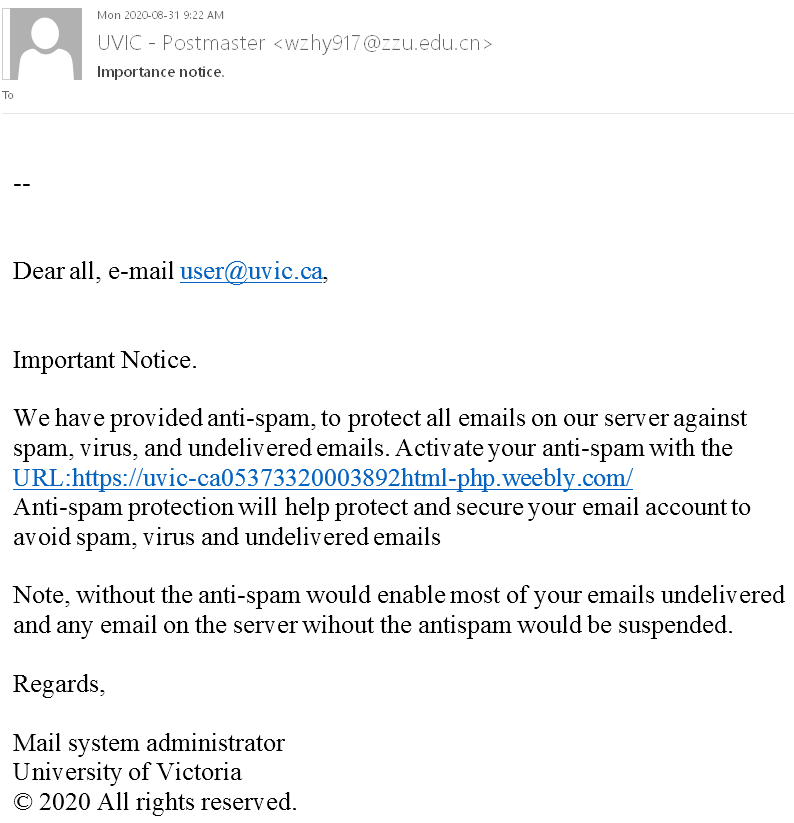
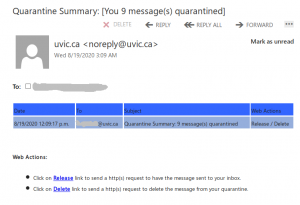
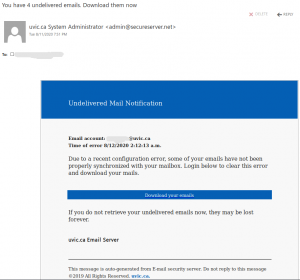
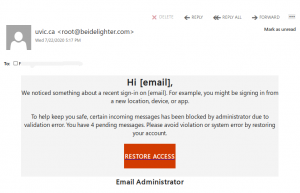
This phish was received by UVic users today. It tries to persuade the victim there was a “configuration error” and as a result some mails could not be delivered. The goal is the same – to make you click on a malicious link which opens a fake OWA page in order to steal your credentials. Please do not click on the link.
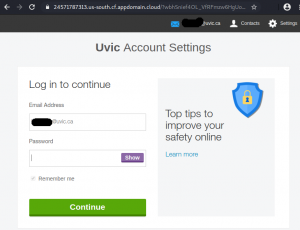
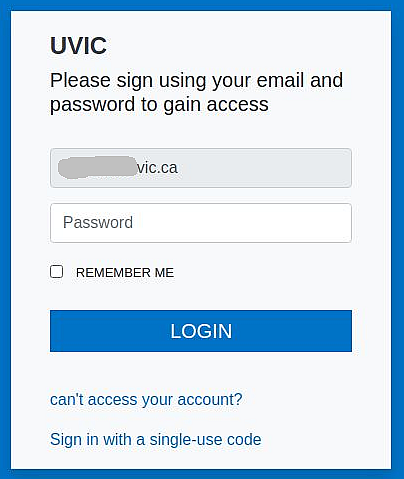
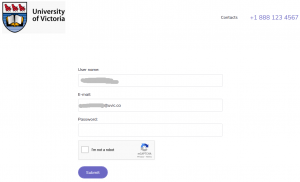
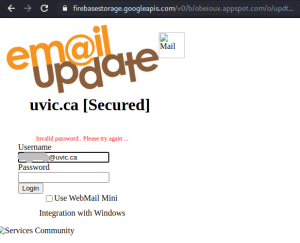
The email and the fake OWA page are shown in the next screenshots:

————————————————————–

 =================================================================
=================================================================
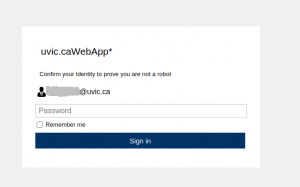
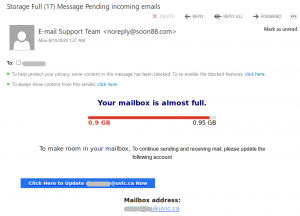
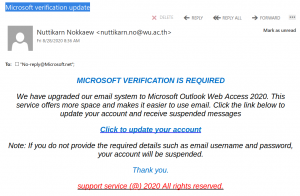 Please do not be curious and do not click on the link. The goal is to steal your UVic credentials (fake Outlook Web App page is shown below). Besides stealing credentials, these pages may contain malware which is why even opening the page is not a good idea.
Please do not be curious and do not click on the link. The goal is to steal your UVic credentials (fake Outlook Web App page is shown below). Besides stealing credentials, these pages may contain malware which is why even opening the page is not a good idea.
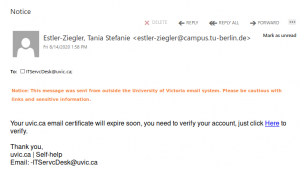
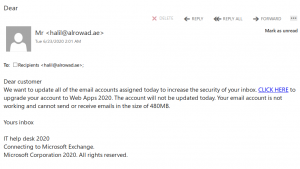
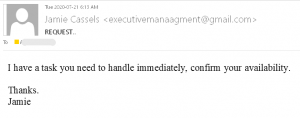 This is a typical start of a gift card scam. We wrote about those back in November:
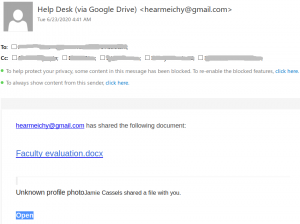
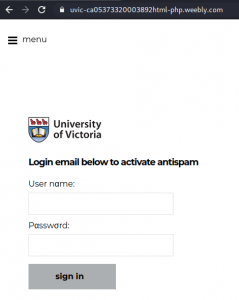
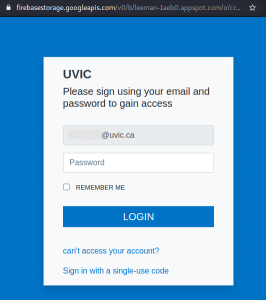
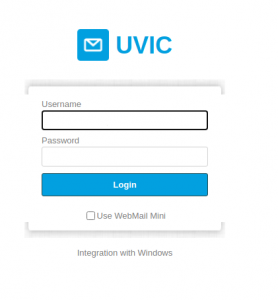
This is a typical start of a gift card scam. We wrote about those back in November: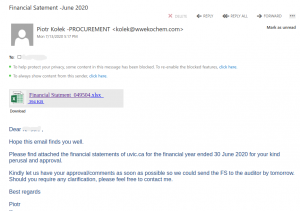 The actual attachment is a html file which redirects the victim to a UVic like OWA page:
The actual attachment is a html file which redirects the victim to a UVic like OWA page: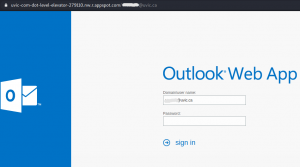 with the intention to steal your credentials. That page is clearly external – look at the address bar in the screenshot.
with the intention to steal your credentials. That page is clearly external – look at the address bar in the screenshot.