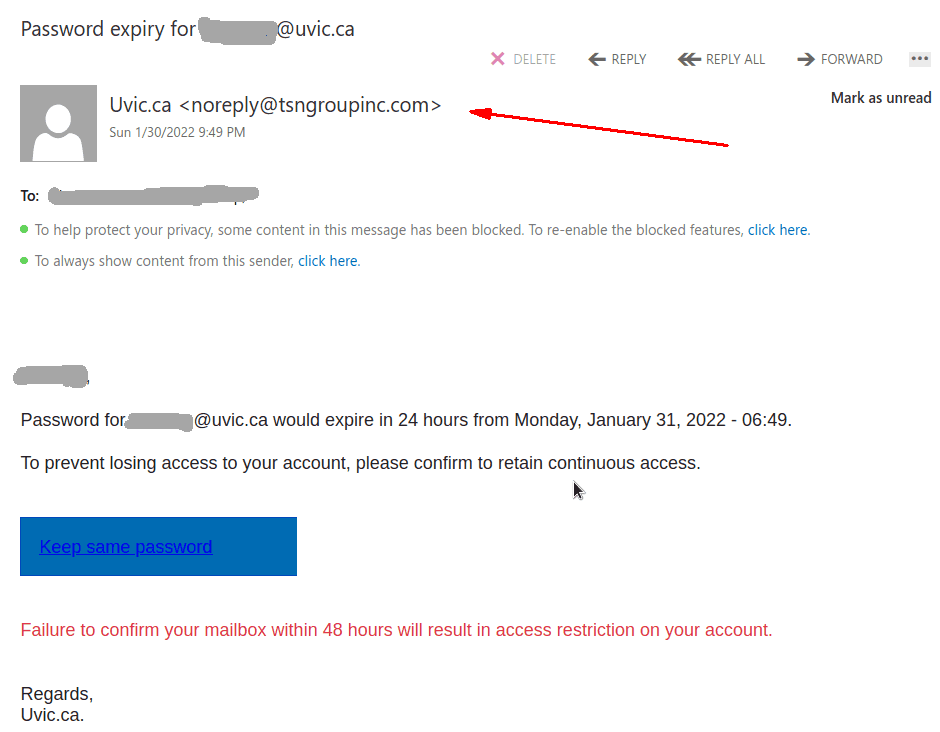
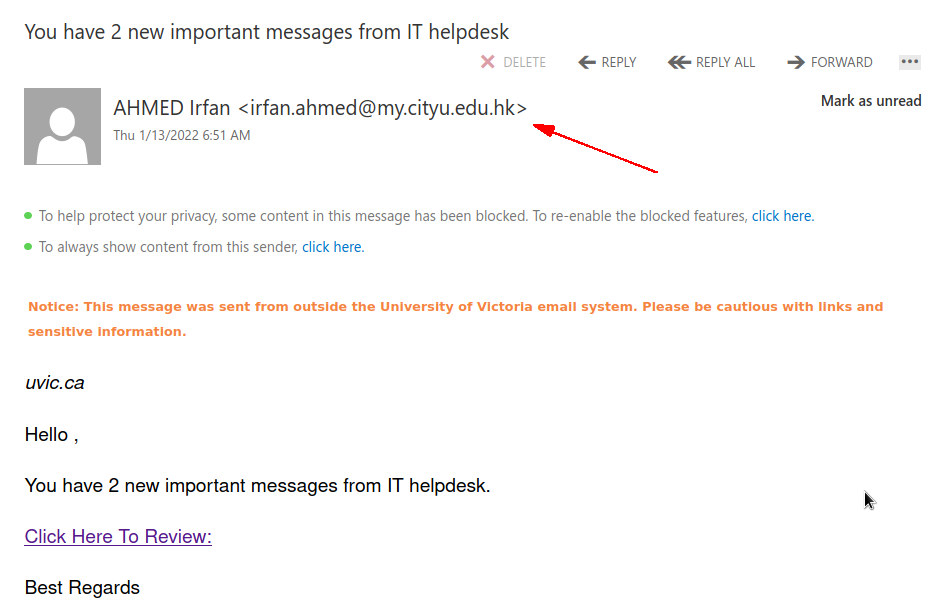
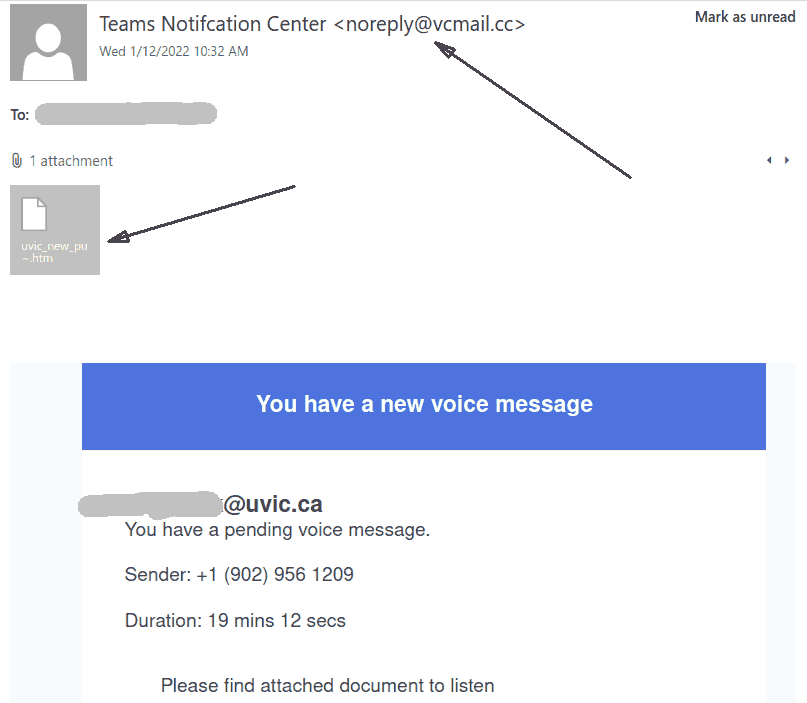
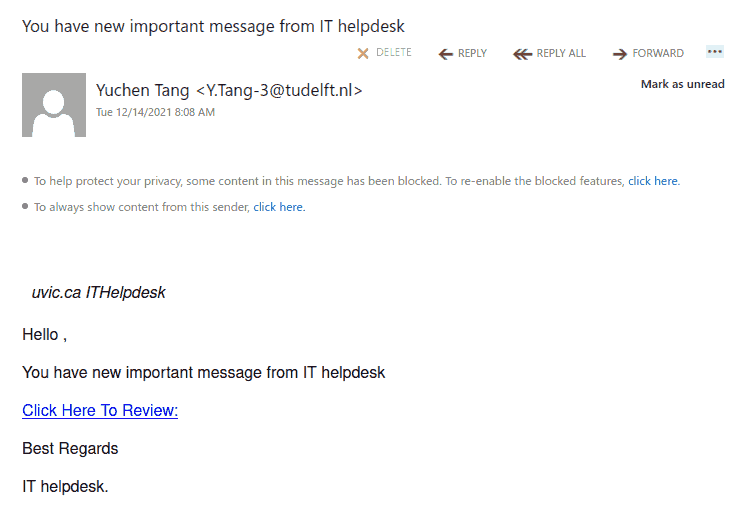
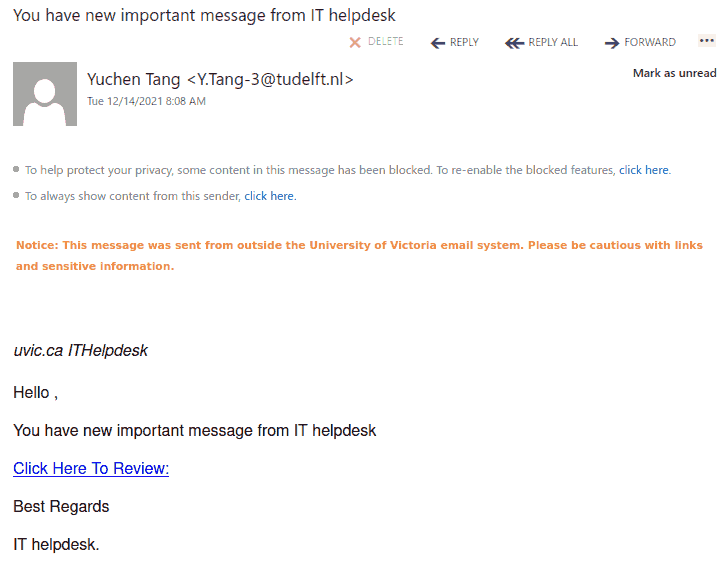
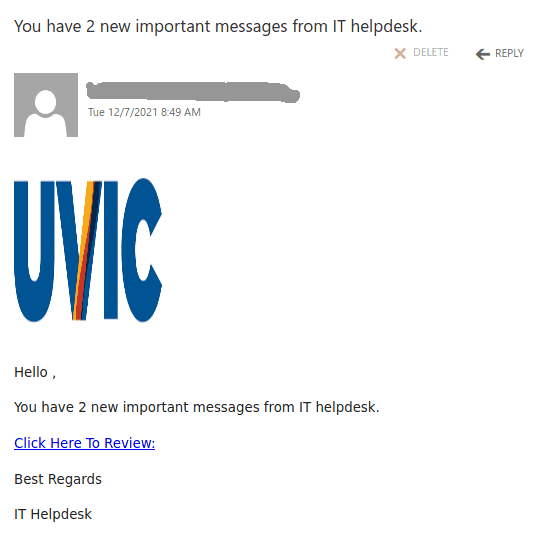
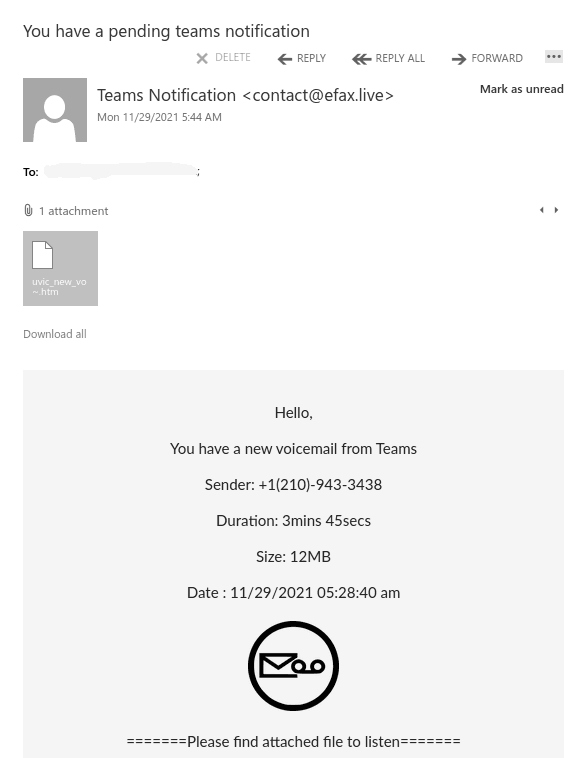
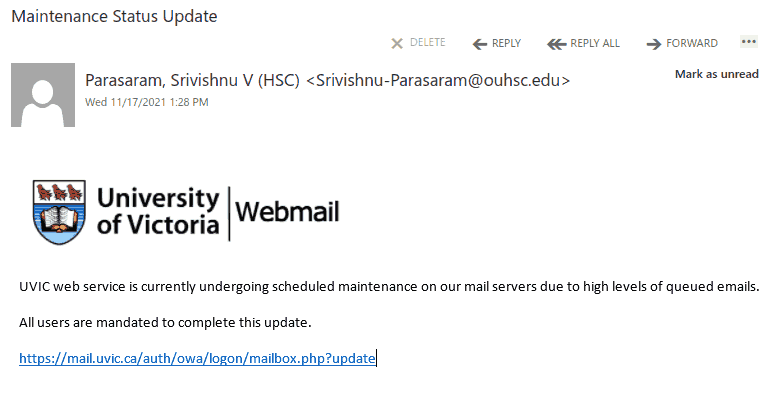
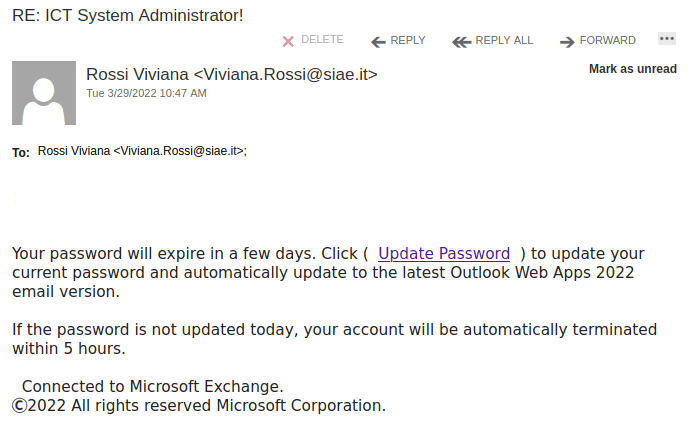
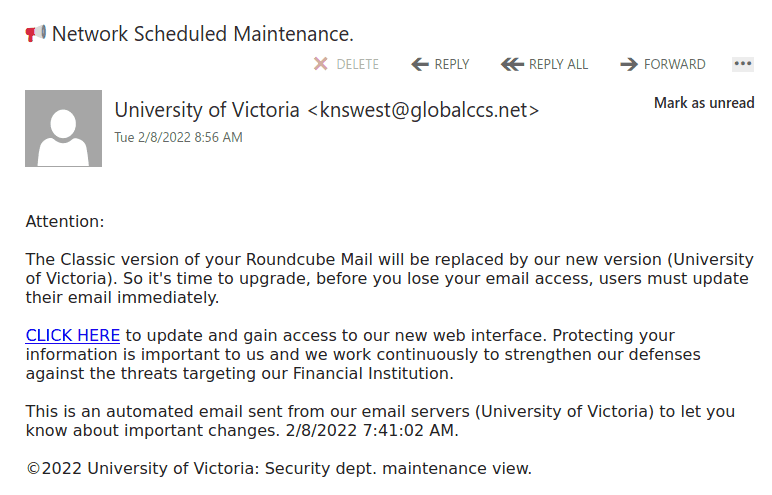
This phish is circulating today.
Same old tactics – scary the user there is something wrong to deal with fast, navigate to a fake page, steal your UVic credentials.
A screenshot of the phish message is shown below. The email of the recipient is included in the message. The links pretend to be internal but in fact point to an external site (that can be seen when hovering with the cursor above the link, without clicking).
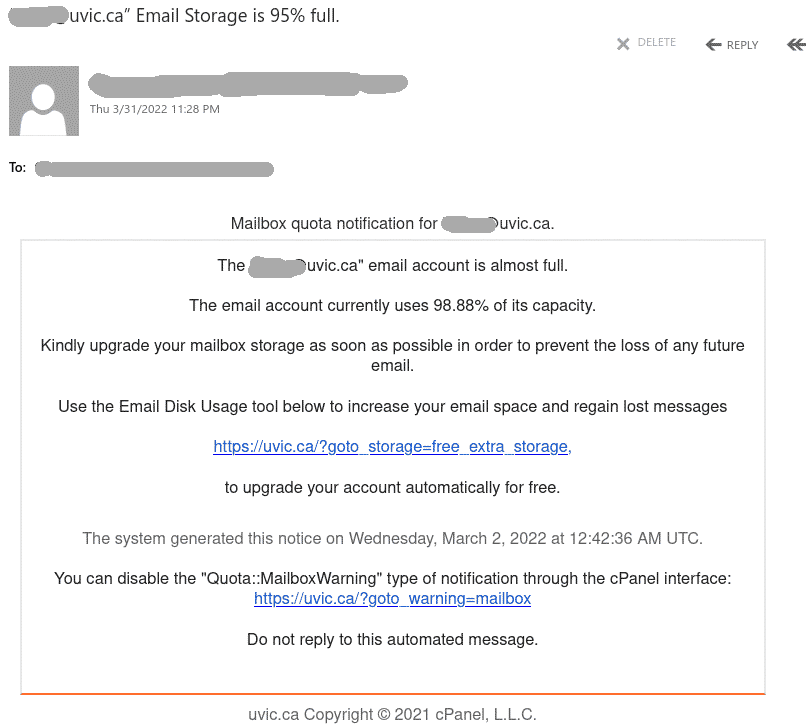
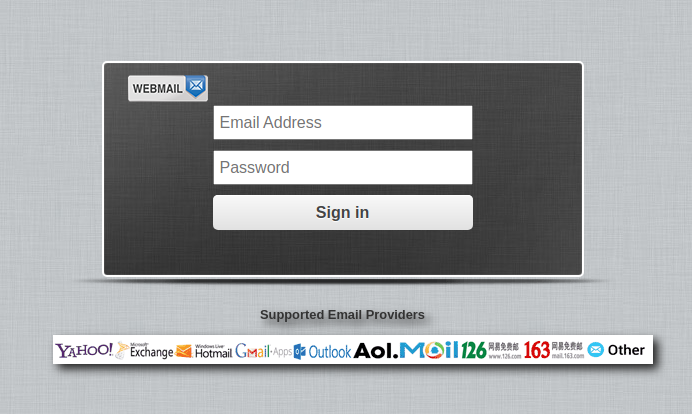
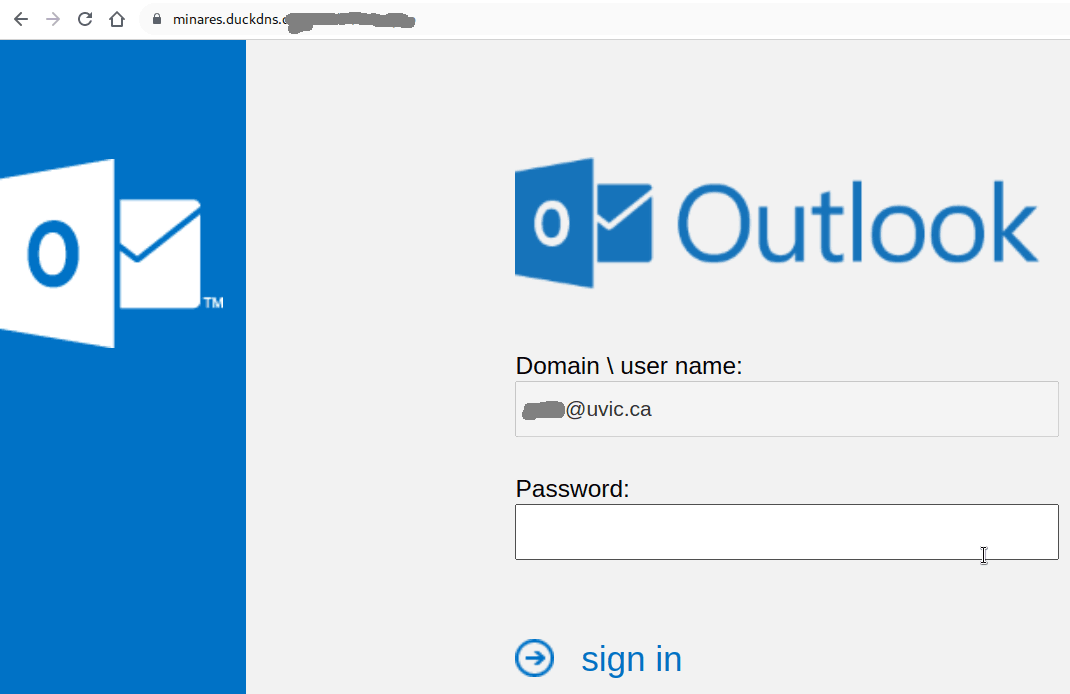
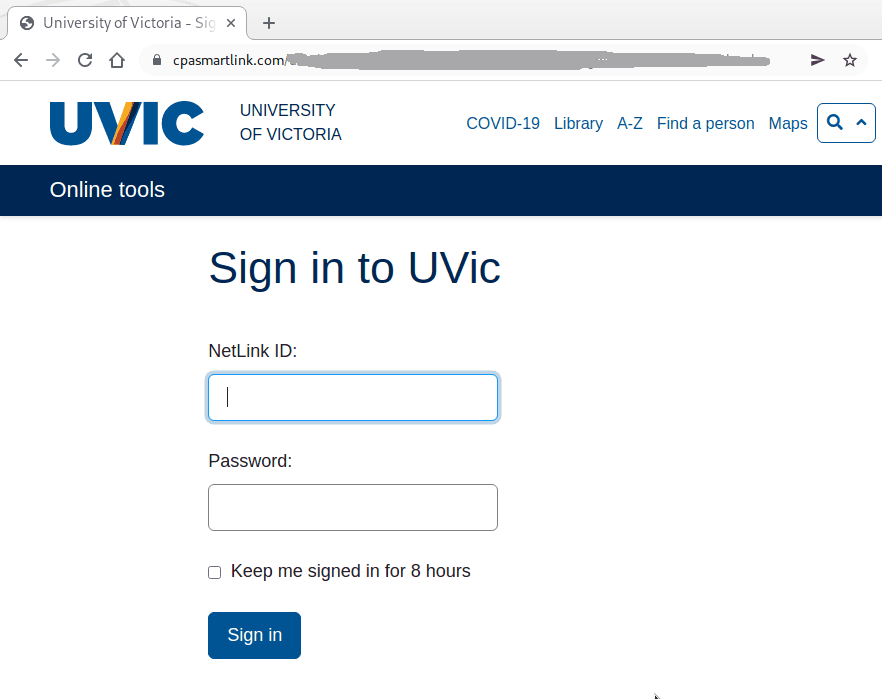
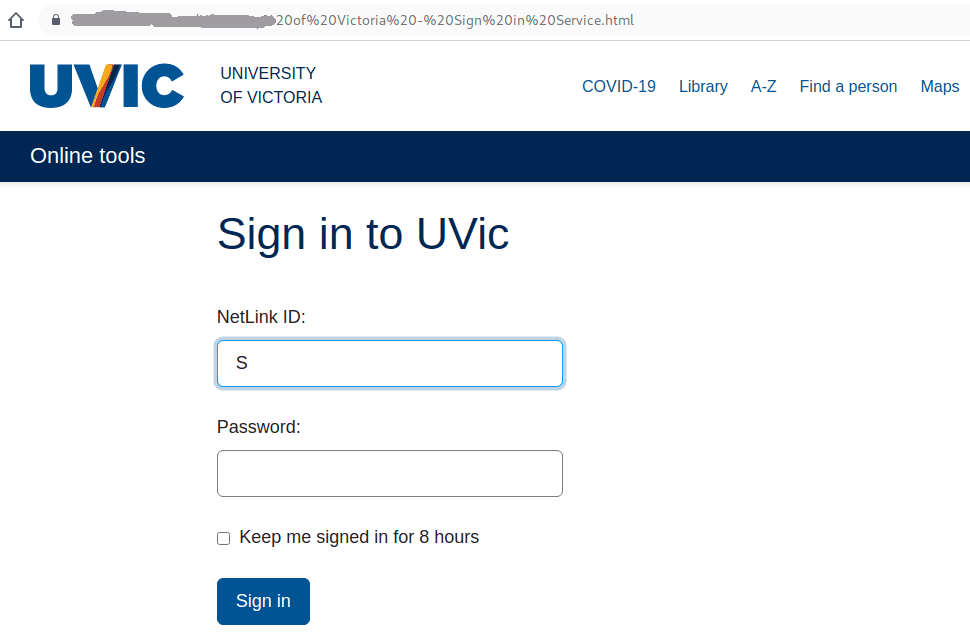
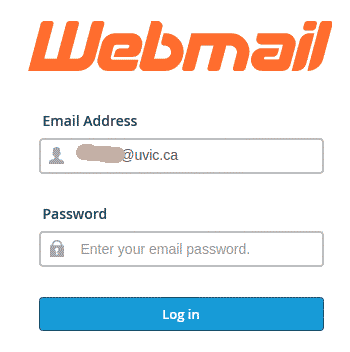
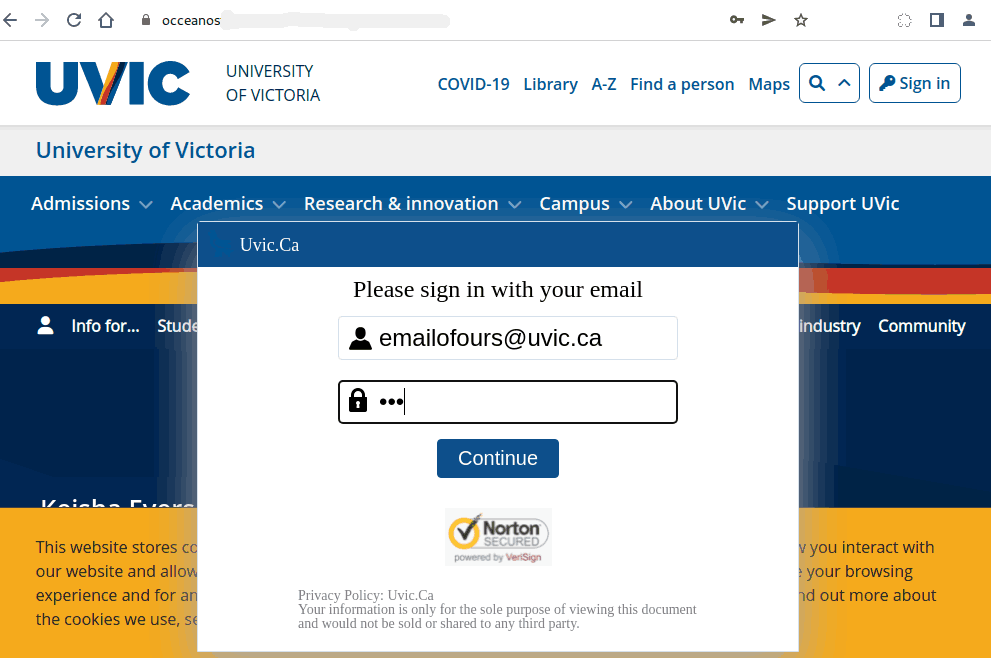
This is how the fake page looks like:



 ——————————————————————————–
——————————————————————————– ———————————————
———————————————