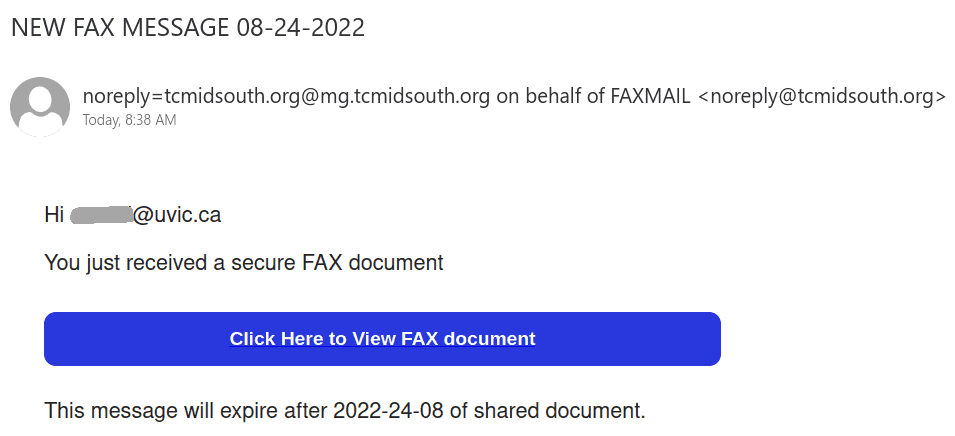
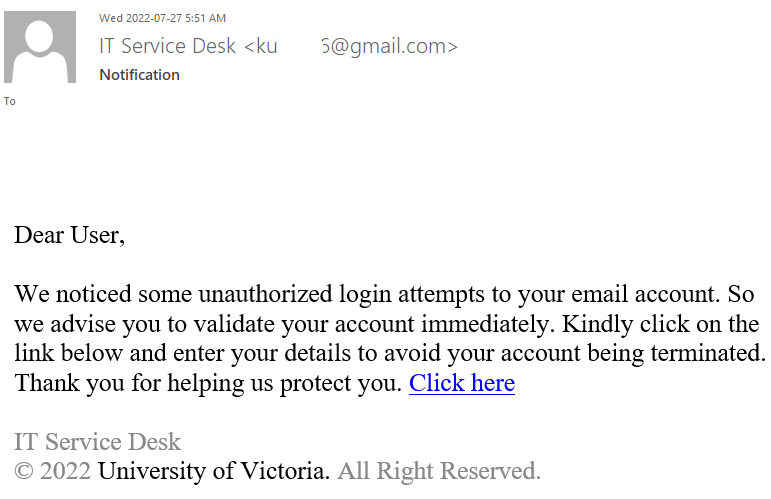
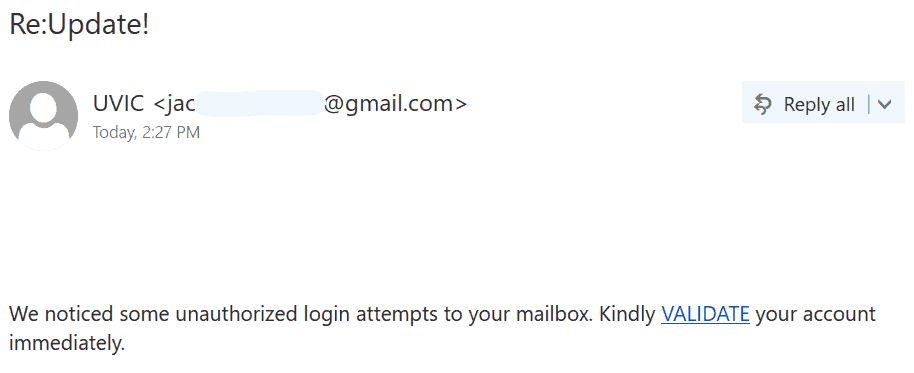
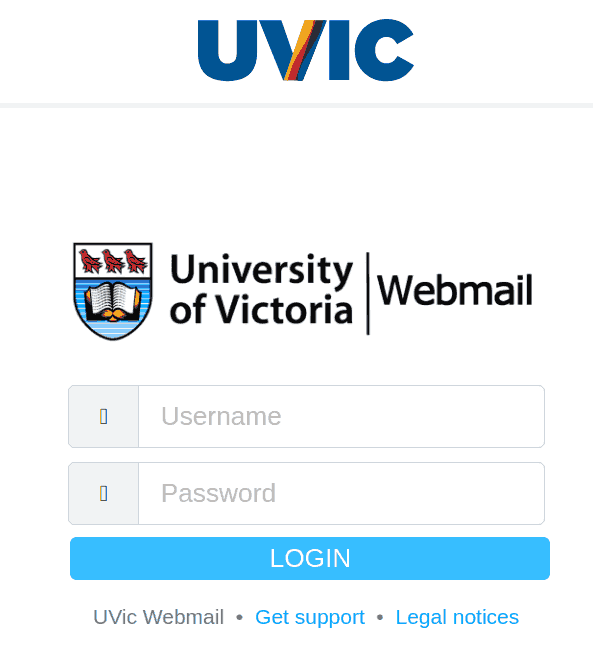
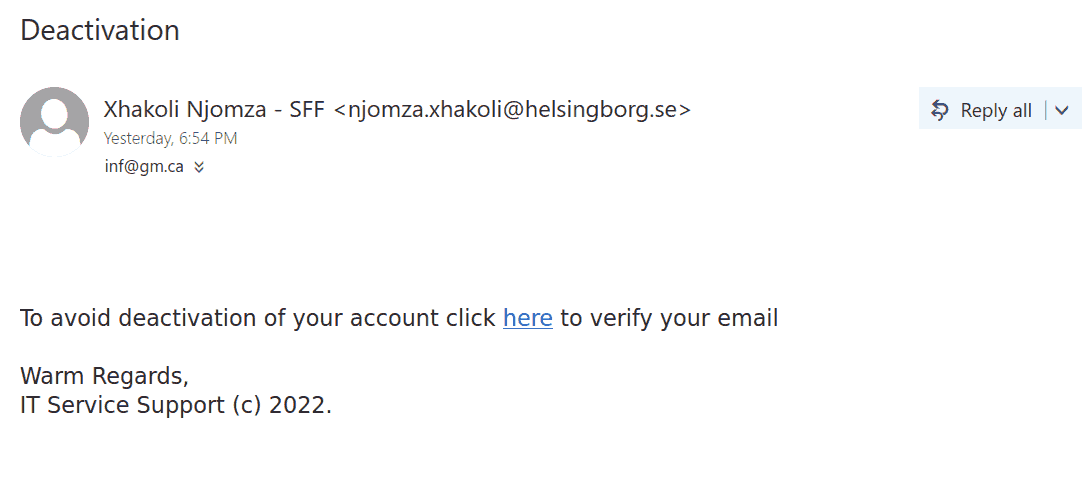
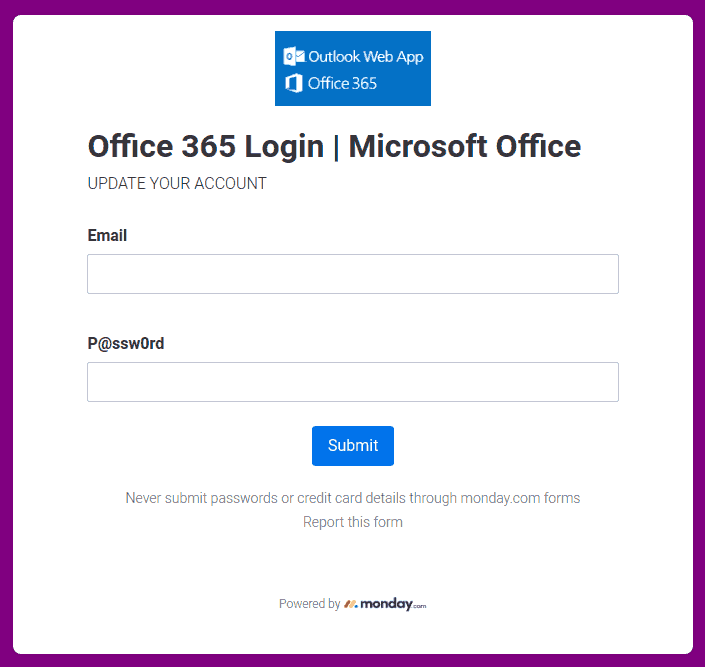
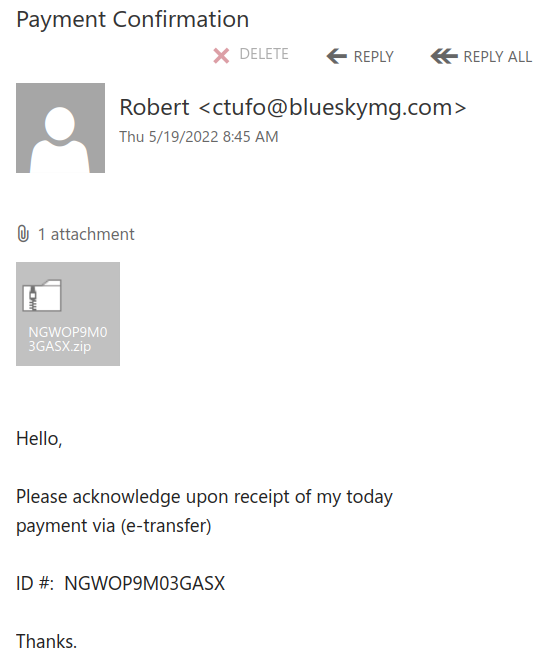
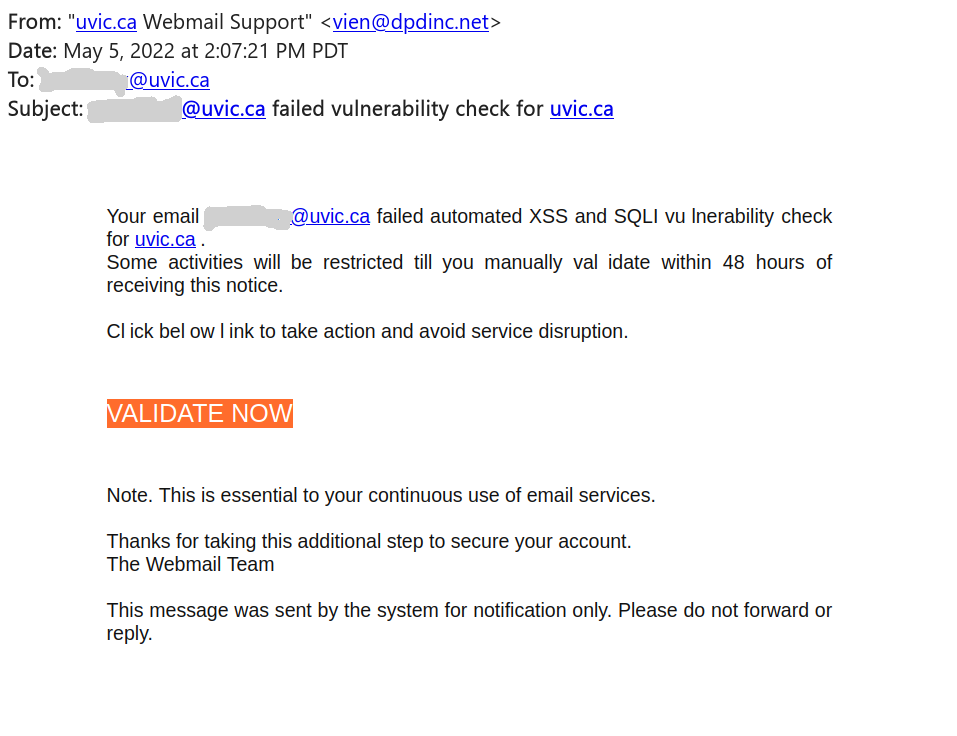
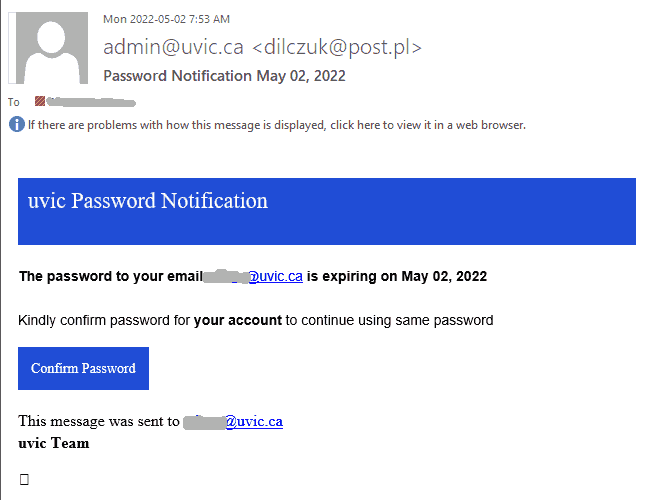
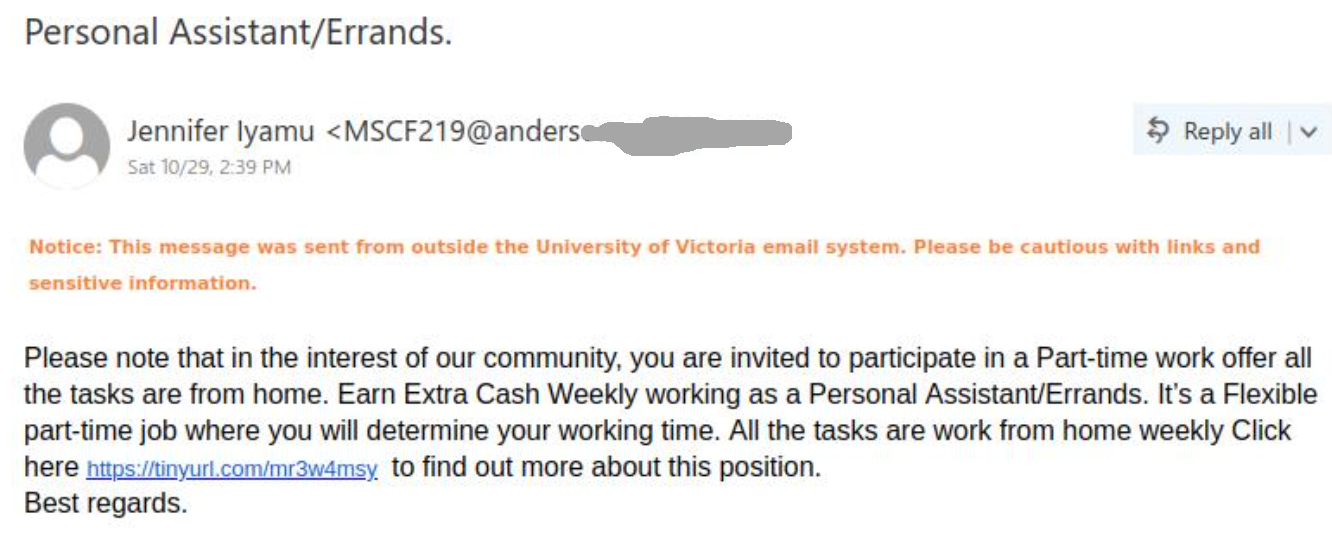
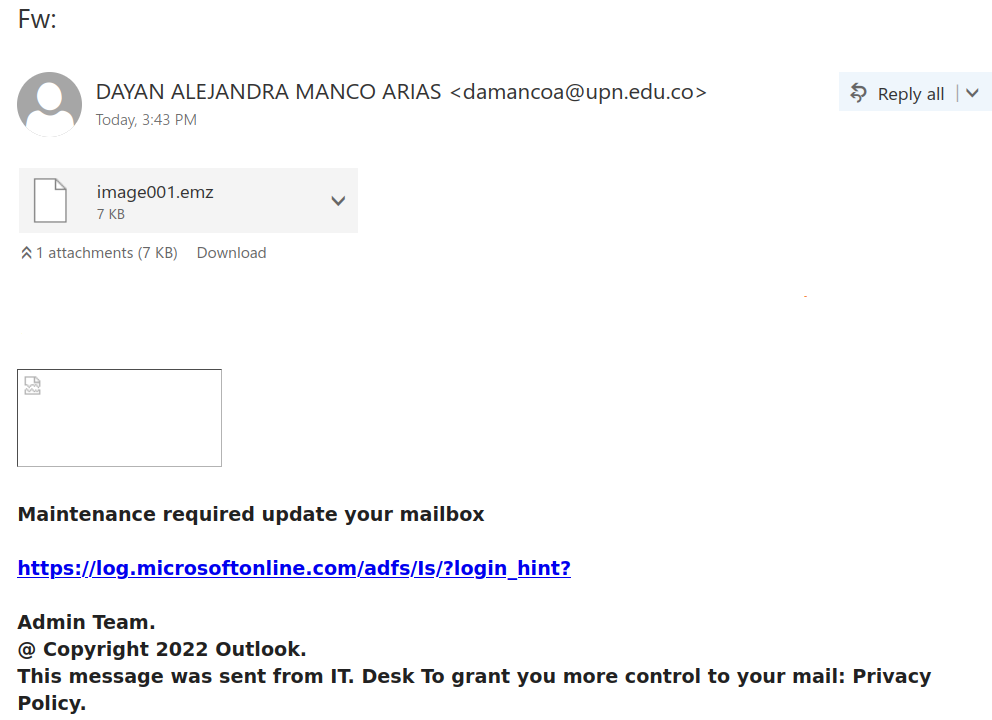
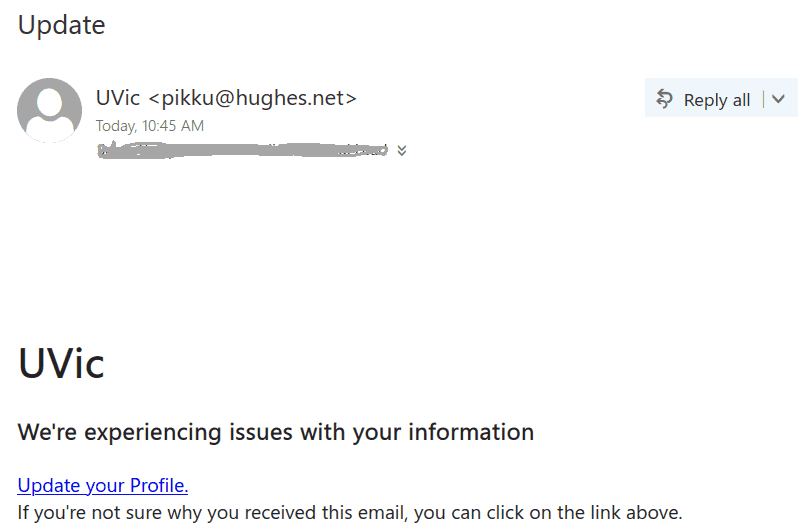
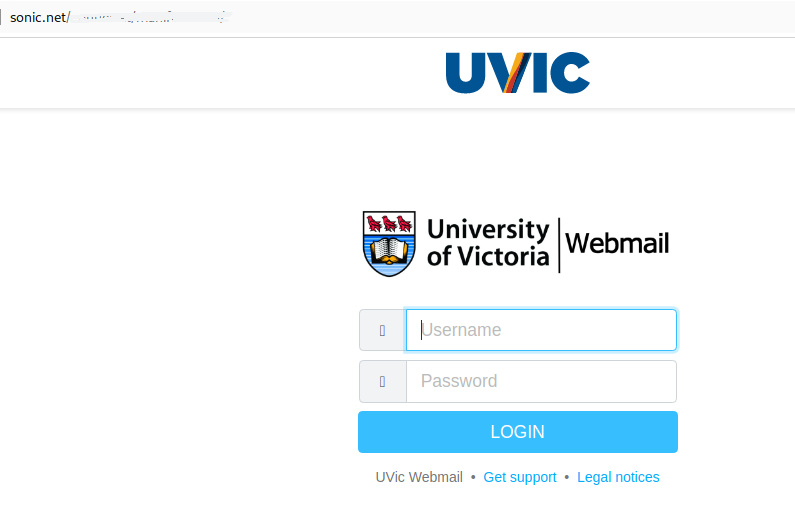
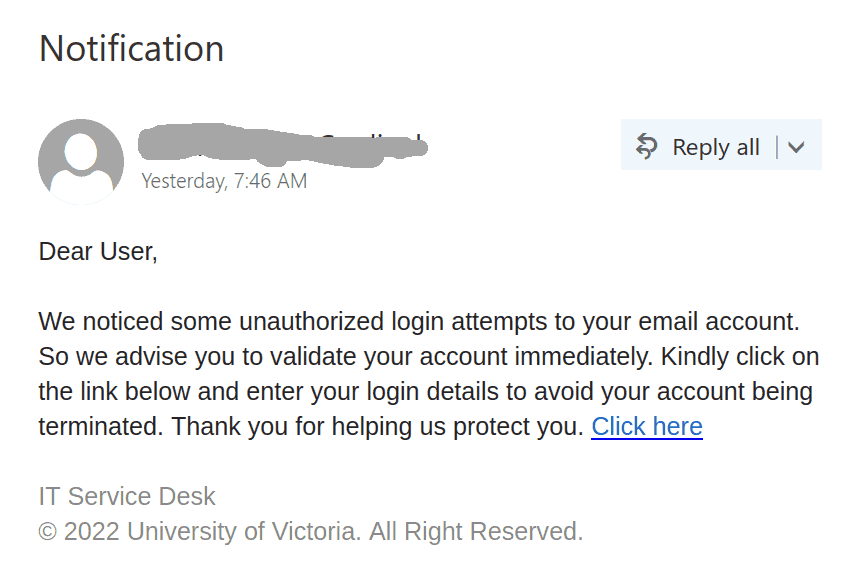
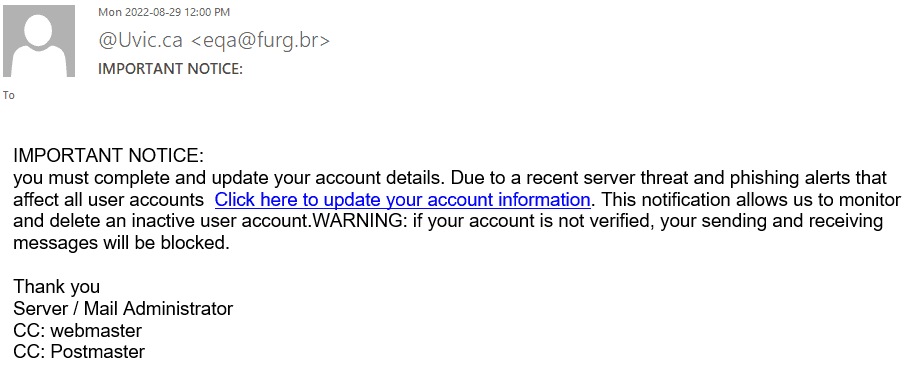
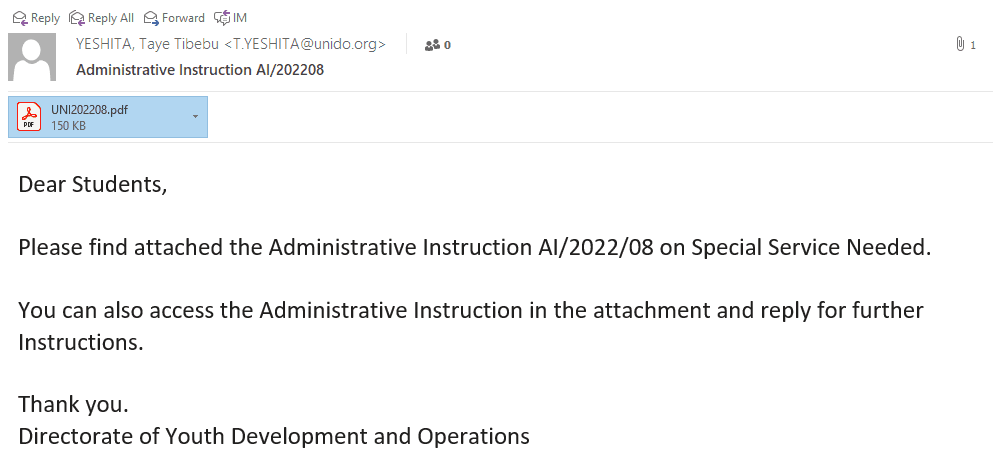
This scam is circulating today. The sender is some external compromised account (but could be any).
Whether a scam that would eventually try to extract money or a phish that aims to steal your credentials, our advice remains the same – never answer by email and never open the links – they may contain malware to infect your computer instantly. Our experts open these in dedicated isolated environments.

 ——————————————————————————
——————————————————————————