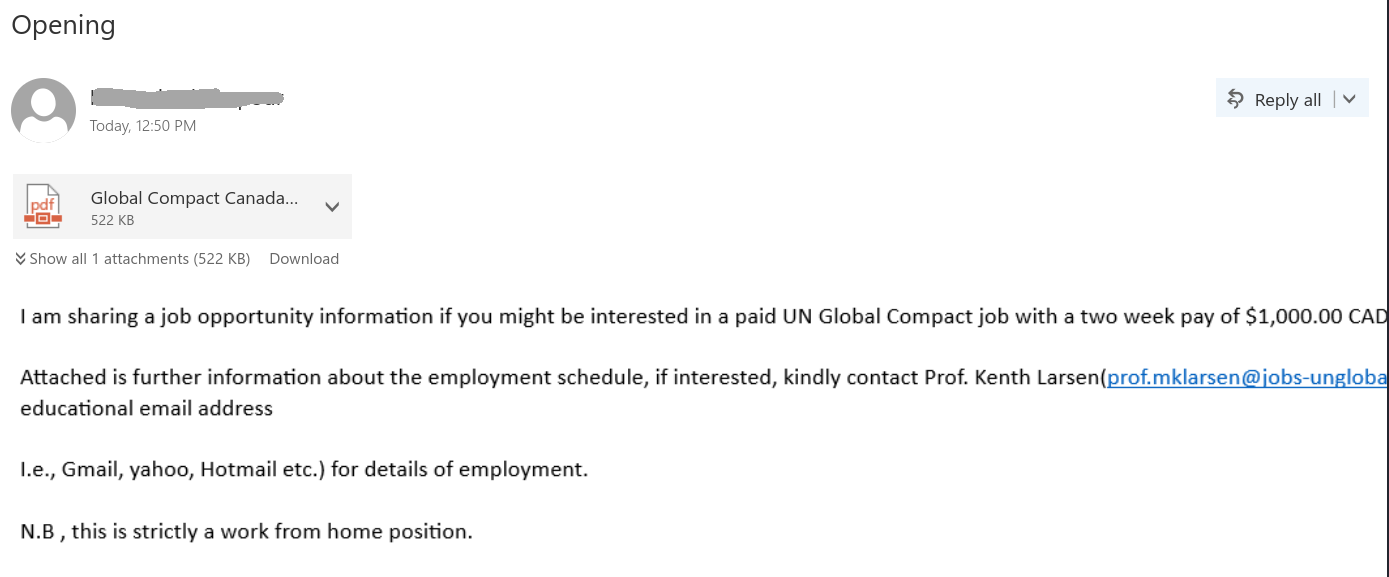
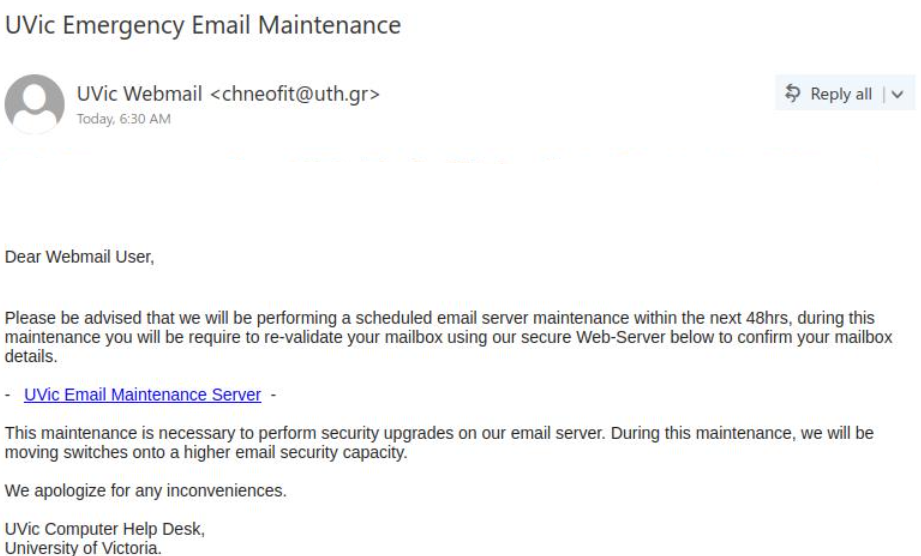
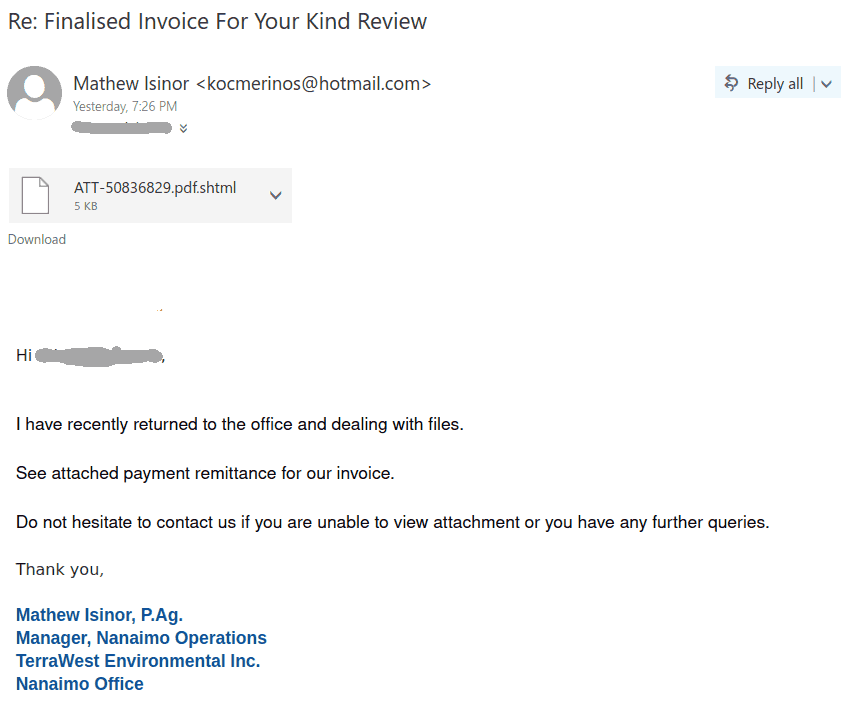
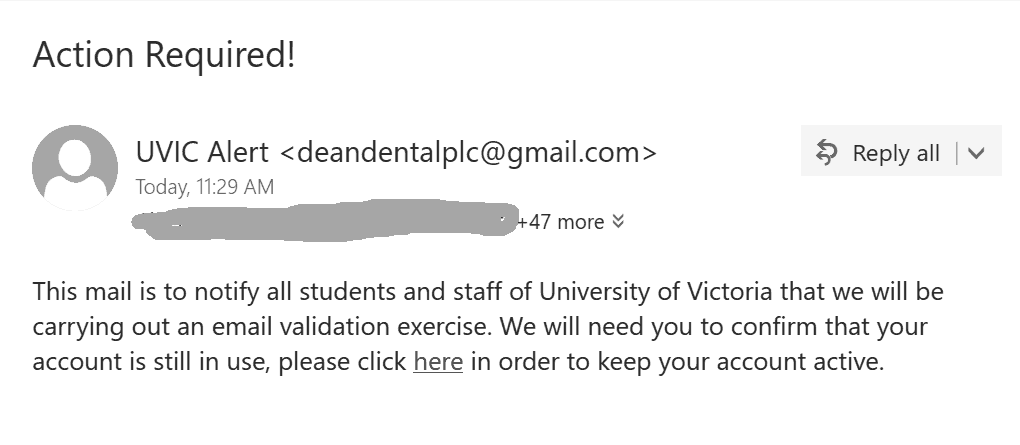
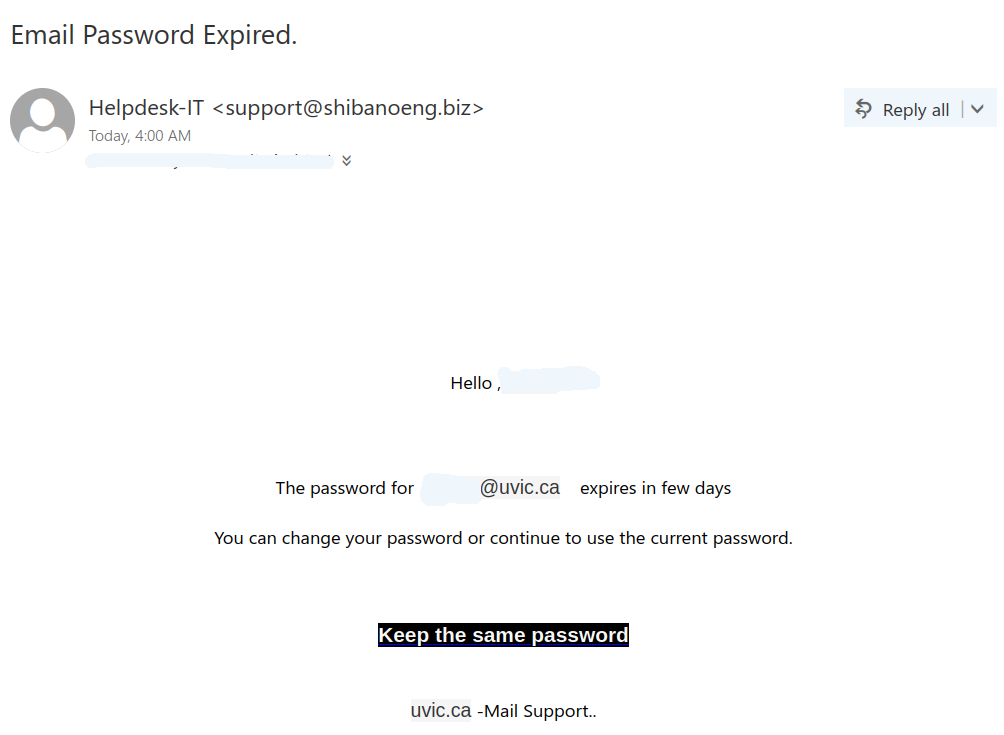
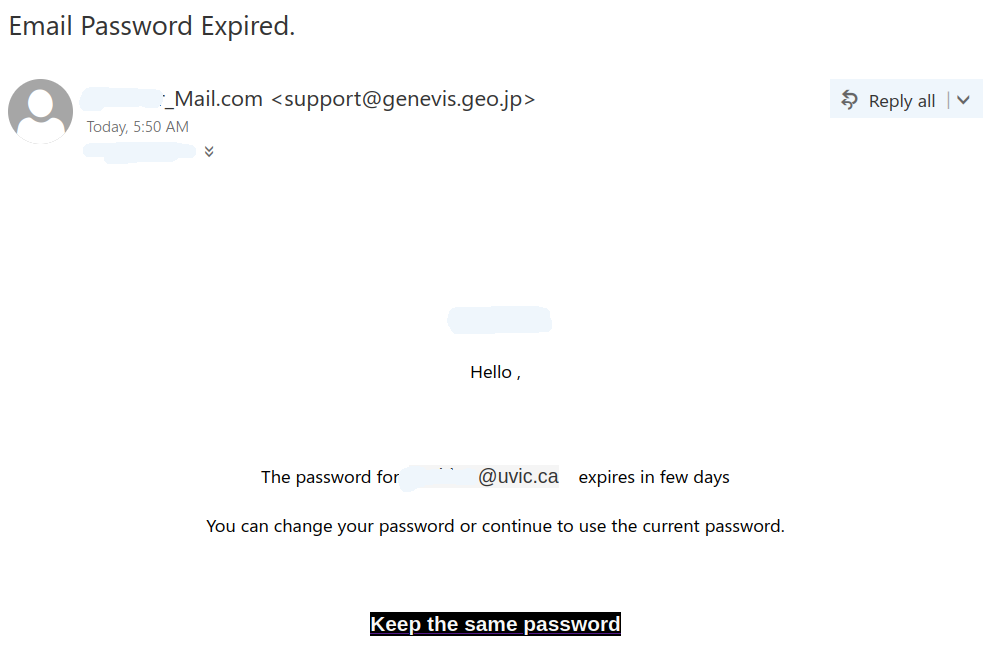
This is another very “popular” phish today.
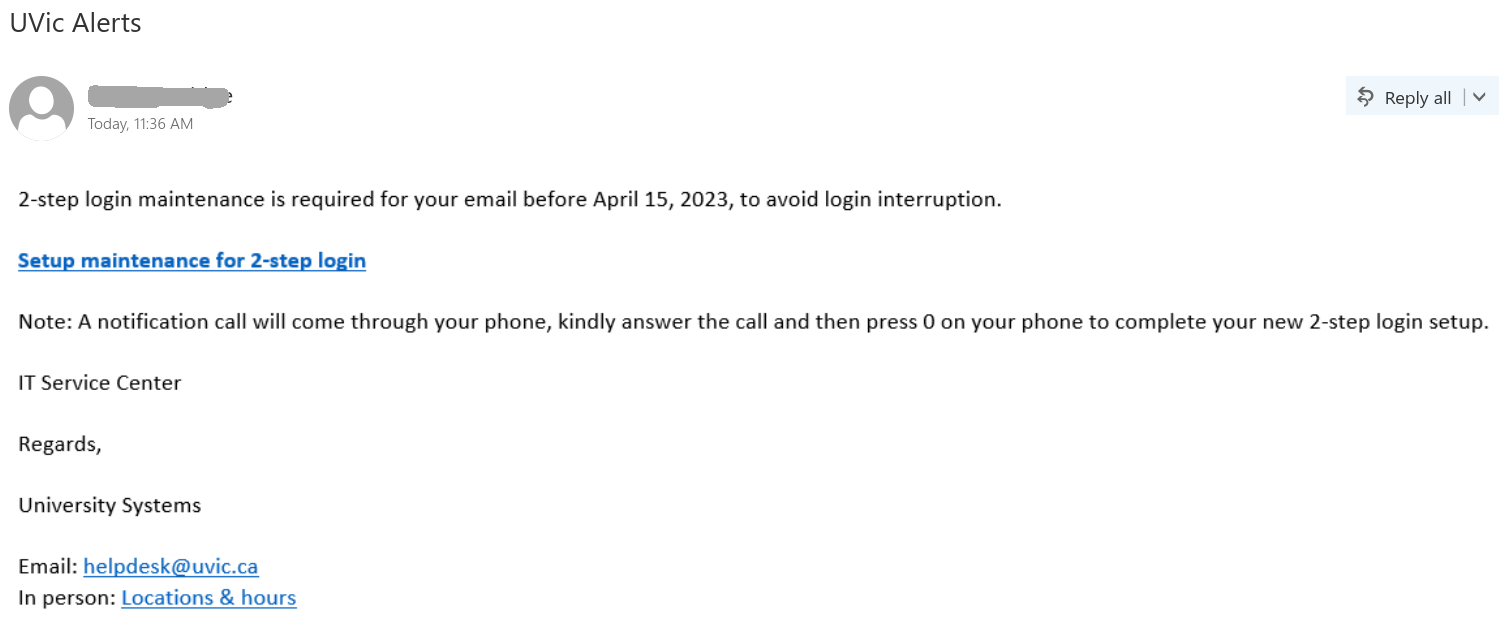
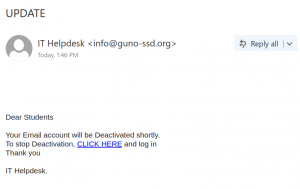
It made effort to sound legit, it contains helpdesk@uvic.ca at the bottom and the sender may appear as an internal one to add to the sense of legitimacy.
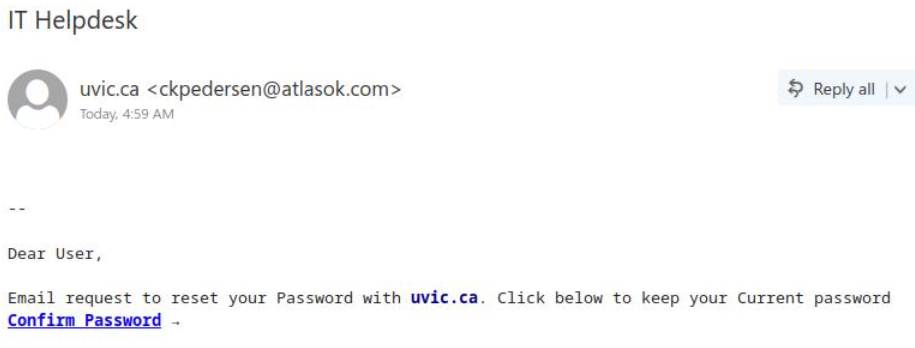
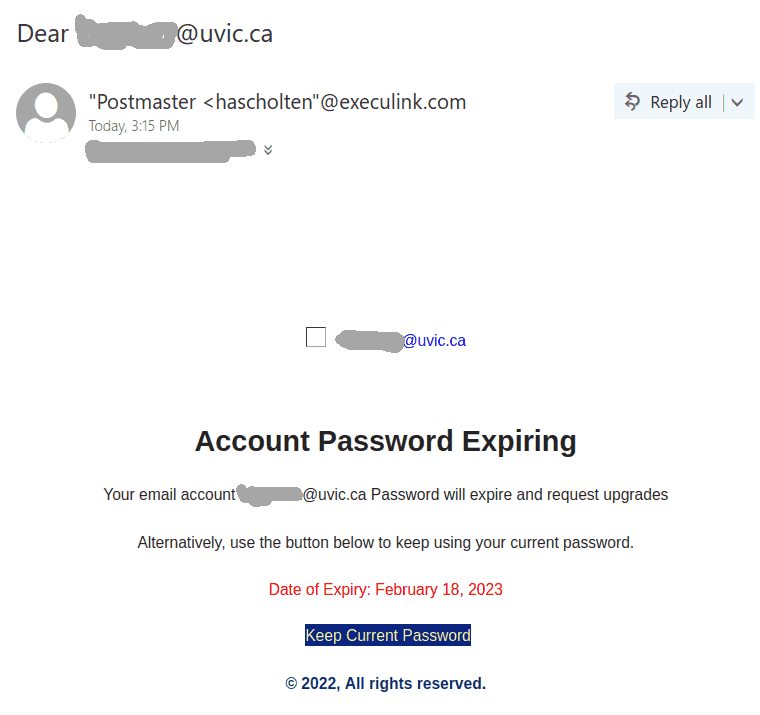
Similarly to the job scam we posted about below, this phish uses the trick to put the whole message in a bitmap. It only looks like text with a link, but the whole body is a single picture. That picture is linked to the malicious website. This way
the victim may click somewhere on what looks like text, thinking it was safe. That would immediately trigger their web browser to open the malicious web page.
Please be careful with clicks and don’t be curious. If in doubt – ask your desktop support person or the Helpdesk.