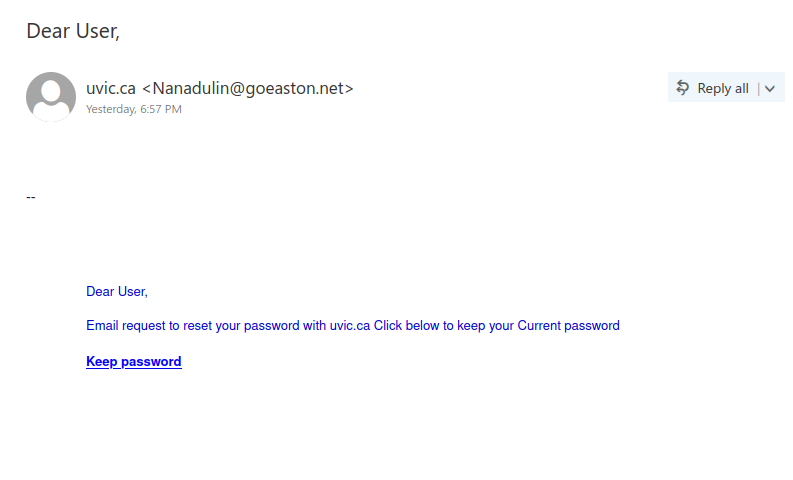
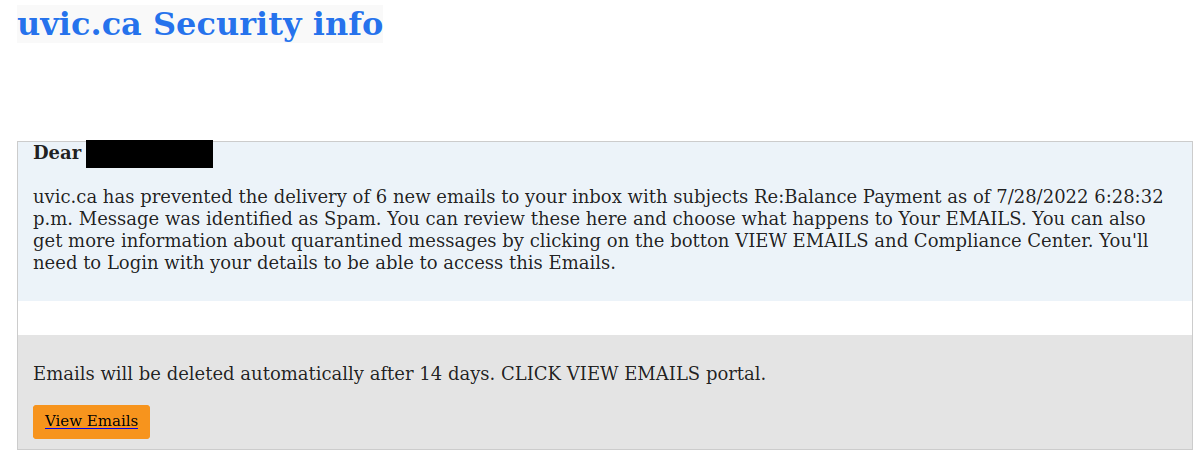
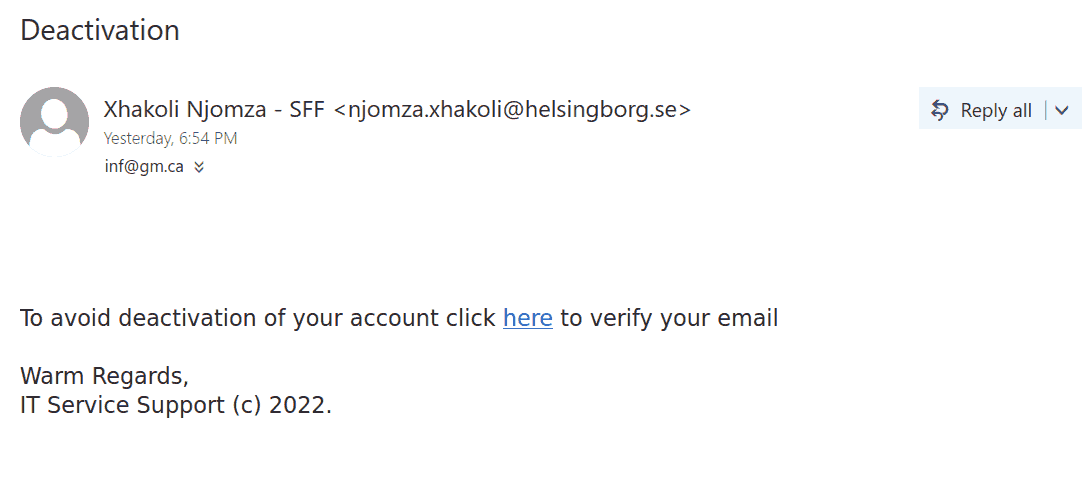
This phish was received by many recipients in our organization last evening.
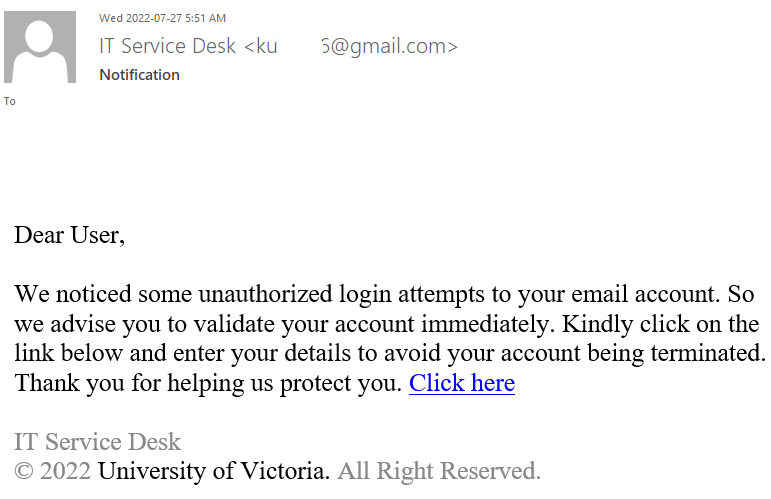
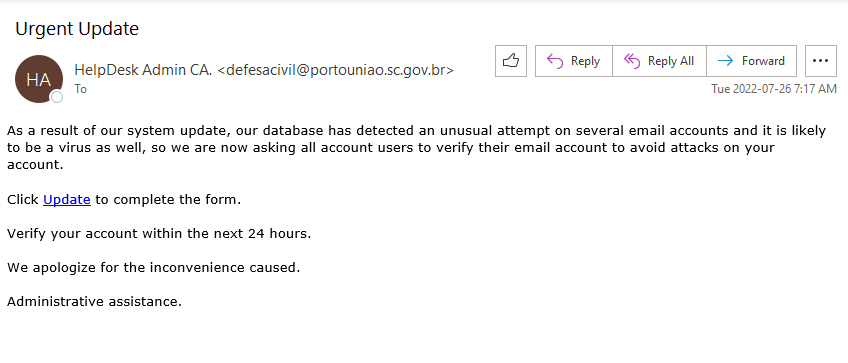
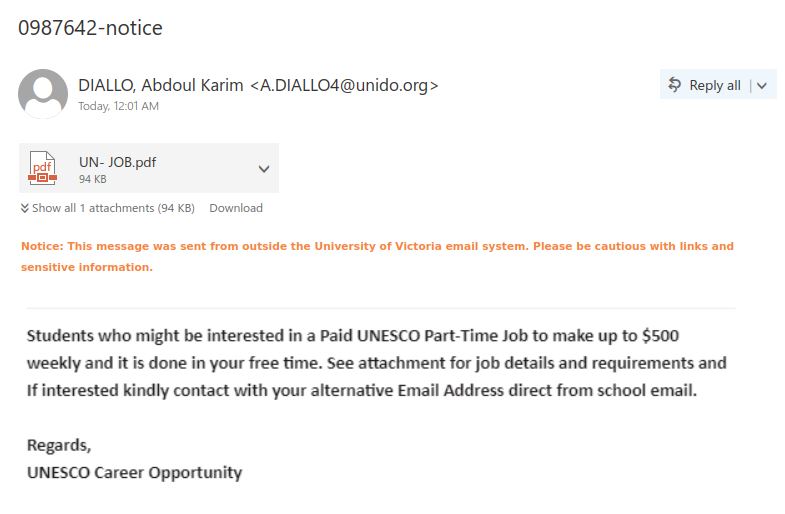
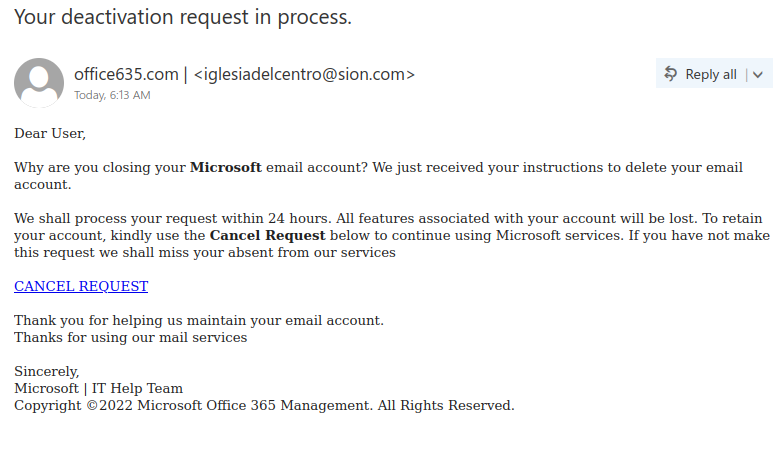
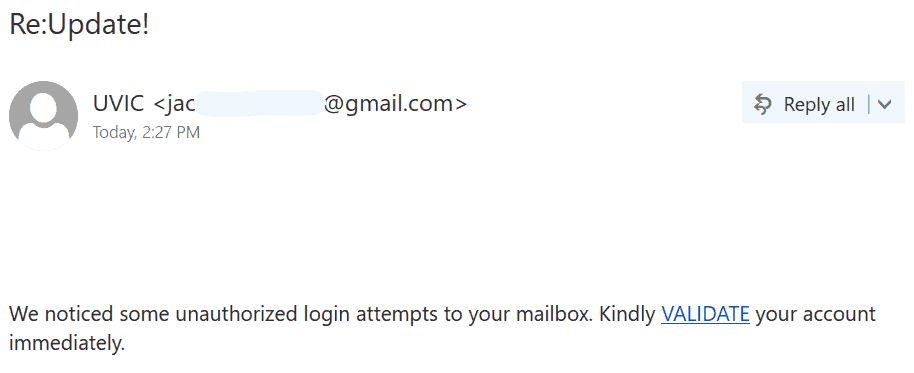
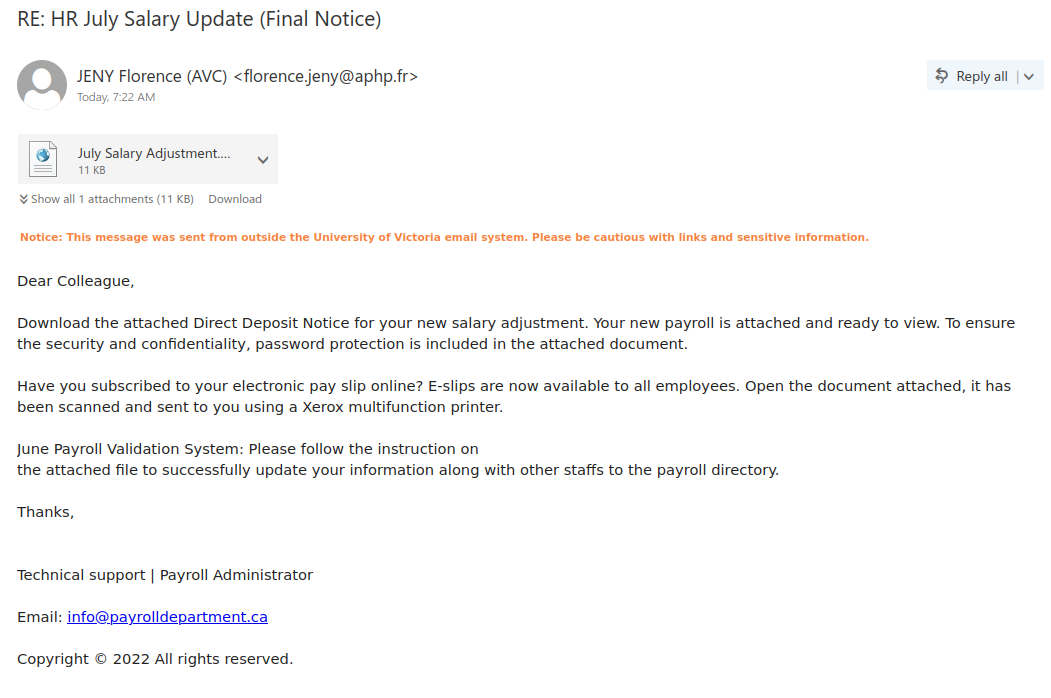
It has usual phishing email signs:
- Subject line doesn’t make sense, salutation is the subject line.
- External Sender (see sender email address) but posing to be ‘uvic.ca’.
- Generic salutation.
- Sense of urgency, reset password was requested but click to keep your current password. Although, the language used is more confusing than urgency but still can lead to hasty actions on recipient’s part.
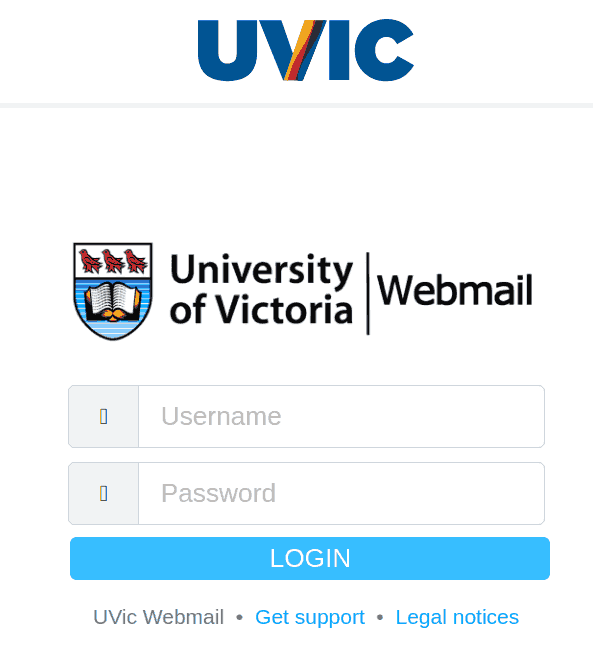
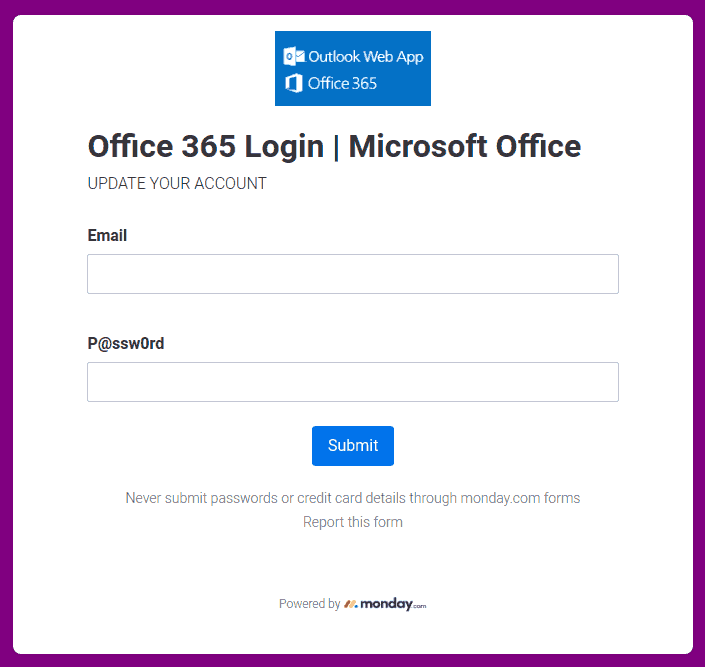
- External link, UVic will never ask you to fill your credentials on external webpage.
If in doubt, better to contact helpdesk or your DSS than clicking on links yourself.