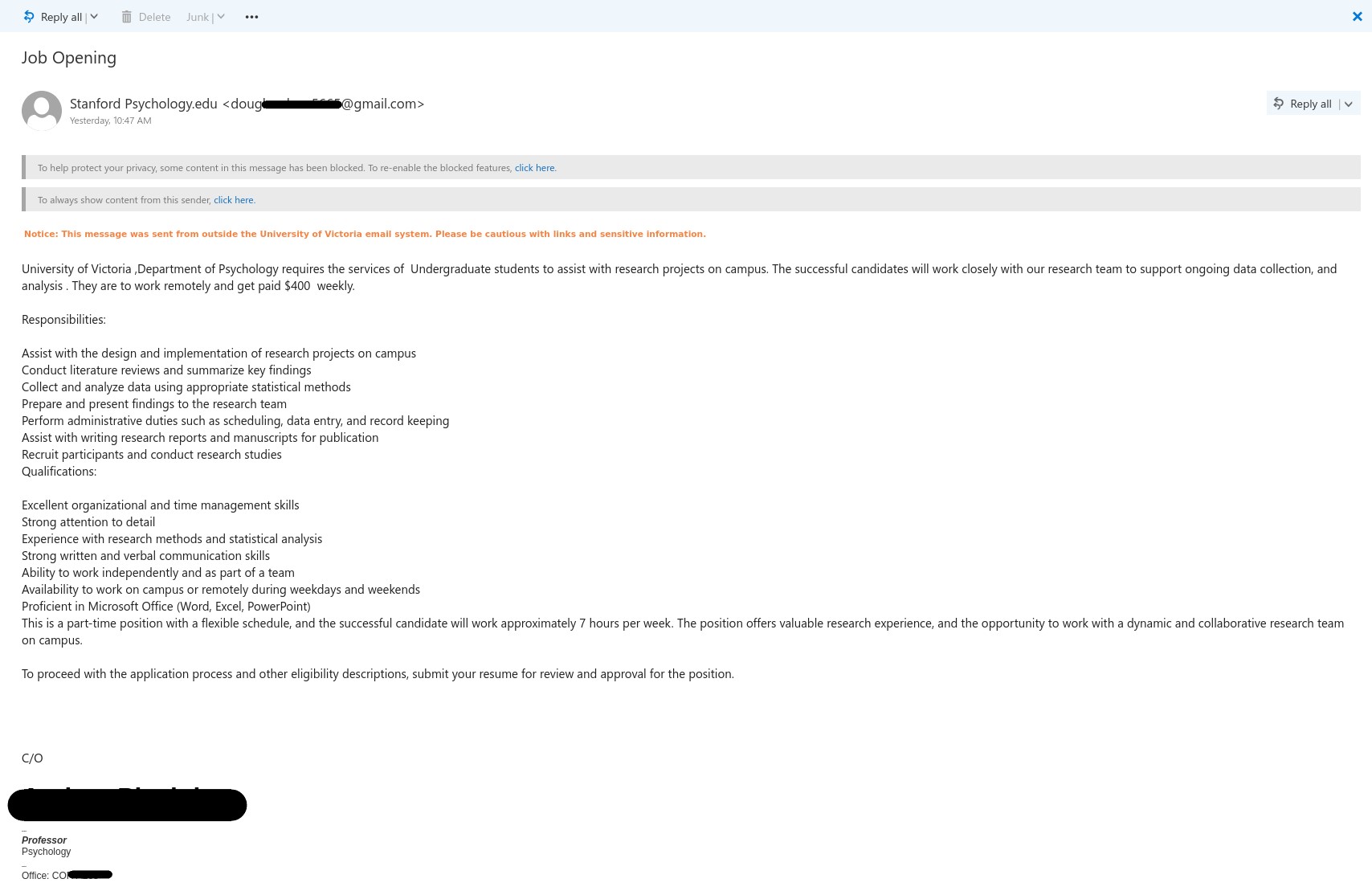
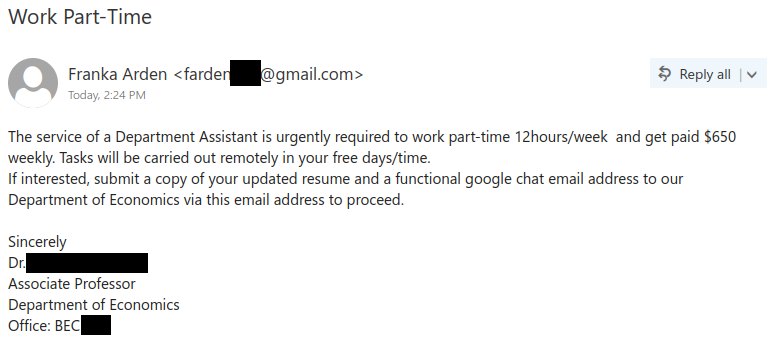
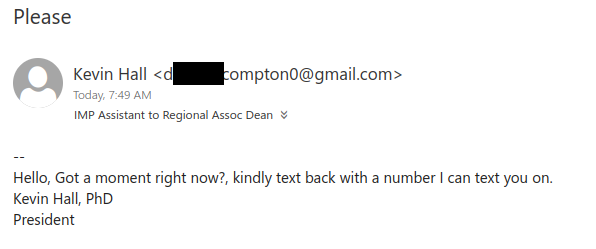
This job scam phish has been circulating today, which spoofs another Canadian institute email. Here is how you can spot this scam:
Please be aware of such scams, always take a moment to look for red flags. In case, you have already fallen for this scam, please immediately stop any further conversation with the scammer and report it to helpdesk or your departmental IT support.
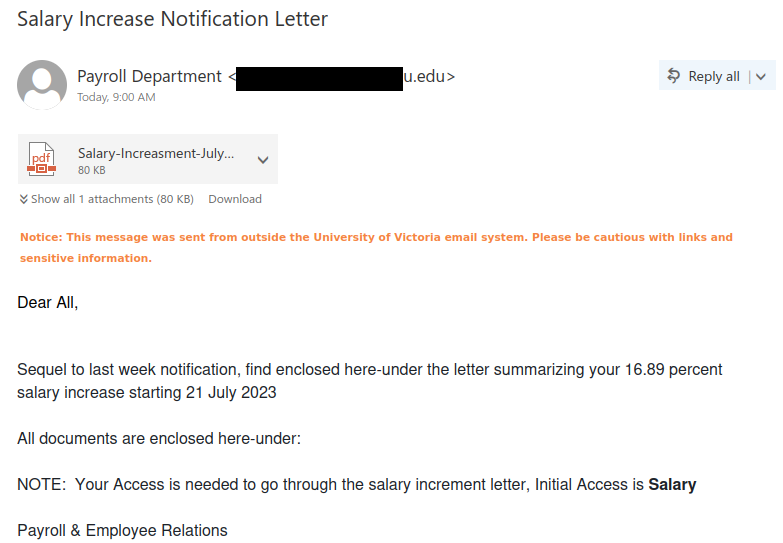
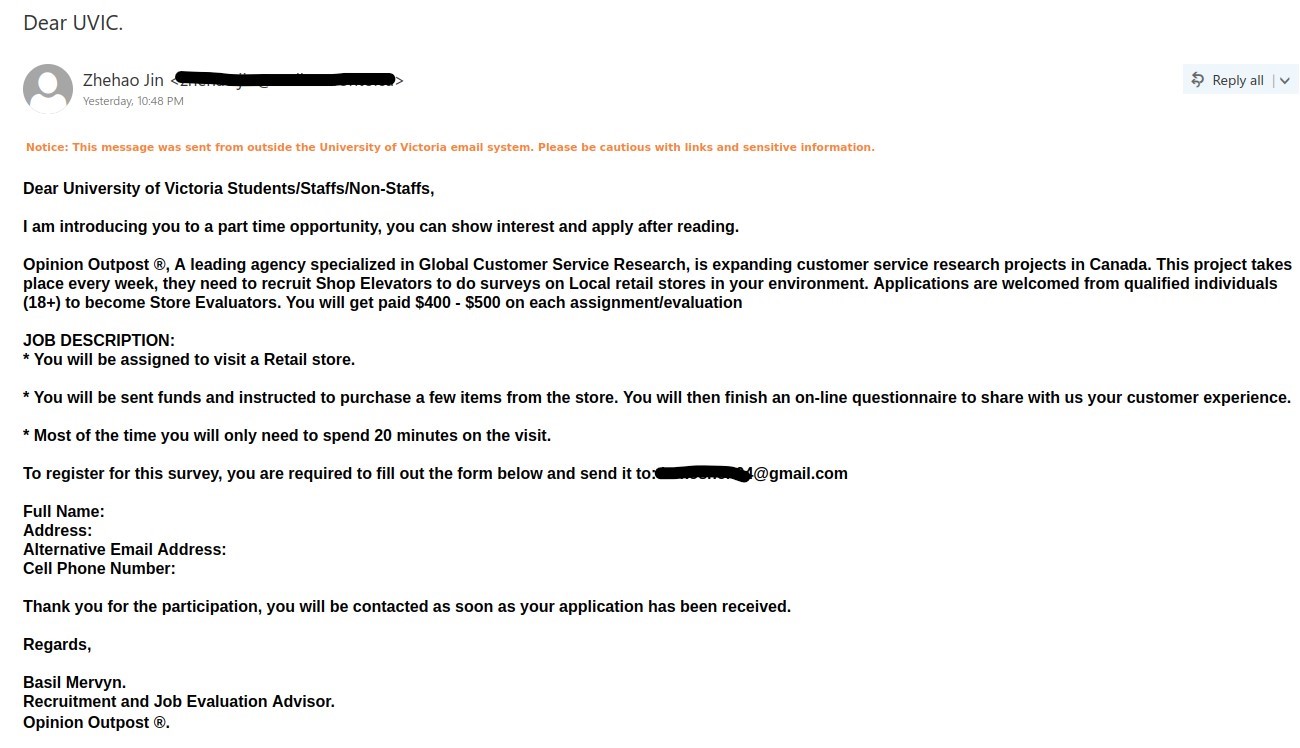
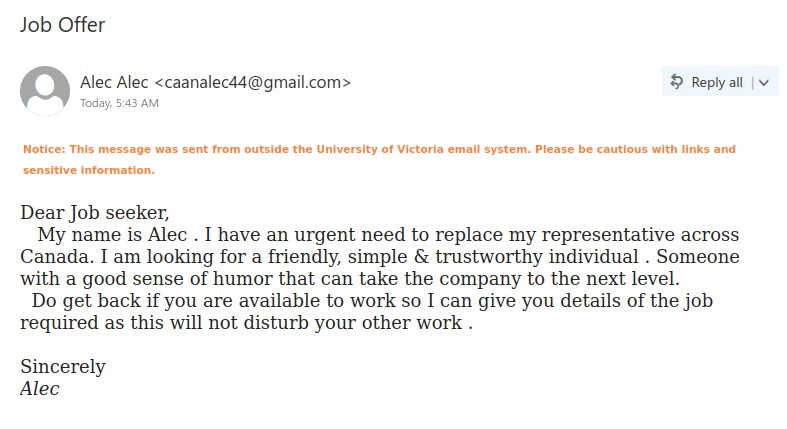
Subject: Dear UVIC.
From: [redacted sender address]
Notice: This message was sent from outside the University of Victoria email system. Please be cautious with links and sensitive information.
Dear University of Victoria Students/Staffs/Non-Staffs,
I am introducing you to a part time opportunity, you can show interest and apply after reading.
Opinion Outpost, A leading agency specialized in Global Customer Service Research, is expanding customer service research projects in Canada. This project takes place every week, they need to recruit Shop Elevators to do surveys on Local retail stores in your environment. Applications are welcomed from qualified individuals (18+) to become Store Evaluators. You will get paid $400 – $500 on each assignment/evaluation
JOB DESCRIPTION:
* You will be assigned to visit a Retail store.
* You will be sent funds and instructed to purchase a few items from the store. You will then finish an on-line questionnaire to share with us your customer experience.
* Most of the time you will only need to spend 20 minutes on the visit.
To register for this survey, you are required to fill out the form below and send it to: [scammer’s gmail address]
Full Name:
Address:
Alternative Email Address:
Cell Phone Number:
Thank you for the participation, you will be contacted as soon as your application has been received.
Regards,
Basil Mervyn.
Recruitment and Job Evaluation Advisor.
Opinion Outpost.