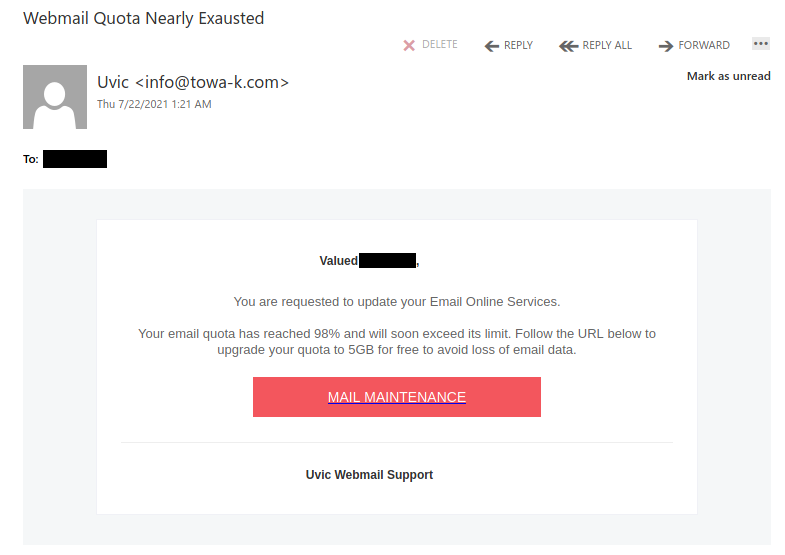
This phish attempts to pose as a UVic Webmail alert, but hovering over the link would clearly show it does not actually go to UVic.
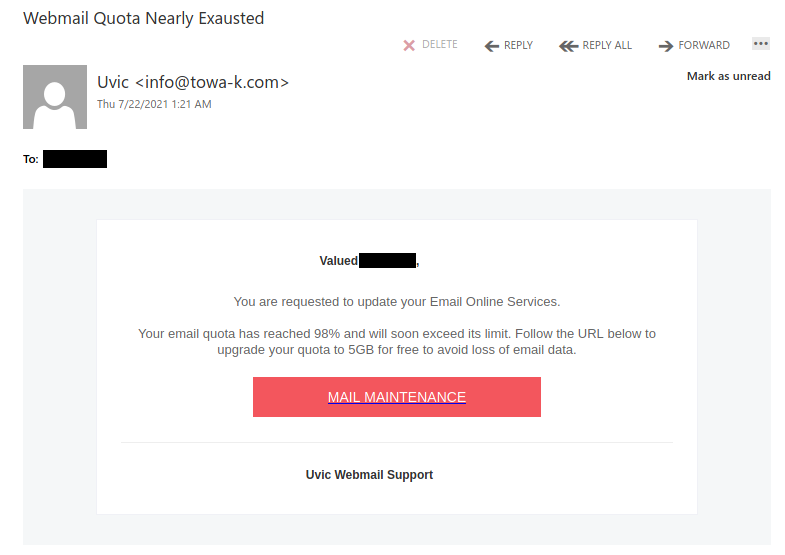
This phish attempts to pose as a UVic Webmail alert, but hovering over the link would clearly show it does not actually go to UVic.
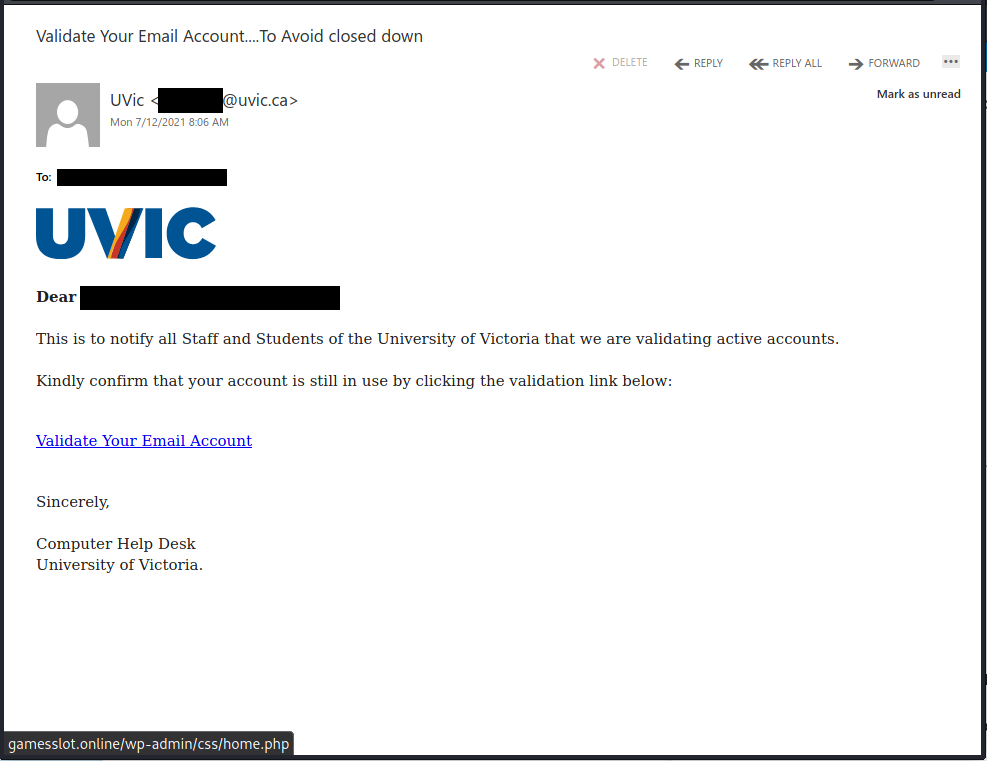
This spear-phishing email used a tailored sender display name, spoofed UVic email address and the UVic logo to make this spear phishing email look more legitimate. Unlike most other phishes, which tend to have a generic signature, the signature block here impersonates the UVic Computer Help Desk.
Though there are other red flags in the email’s contents, the smoking gun is the link–if you hover over it, you can clearly see that it goes to a suspicious non-UVic website (see the bottom of the screenshot). That website hosts a realistic copy of the UVic OWA login page, complete with the policy text. Don’t click on that link or enter your credentials on that page!
If you clicked on the link, contact your department’s IT support staff or the Computer Help Desk immediately.
This phish spoofed the recipient’s email address. It tries to use Microsoft branding to make the email look like a Microsoft Planner notification, even going so far as to make all of the blue links go to legitimate Microsoft Planner pages. However, the green “Open in Microsoft Planner” is a different story–it goes to a feedproxy.google.com URL, which is a red flag in this context.
While feedproxy.google.com itself isn’t a phish site, that service is used to redirect visitors to other sites, so the final destination is likely to be completely different and untrustworthy. The phisher has used a legitimate redirect URL to hide the real malicious destination.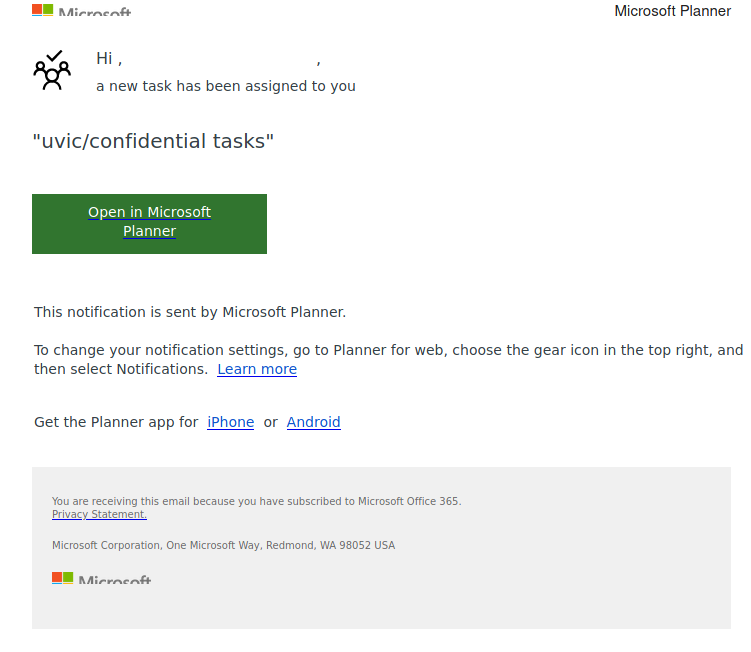
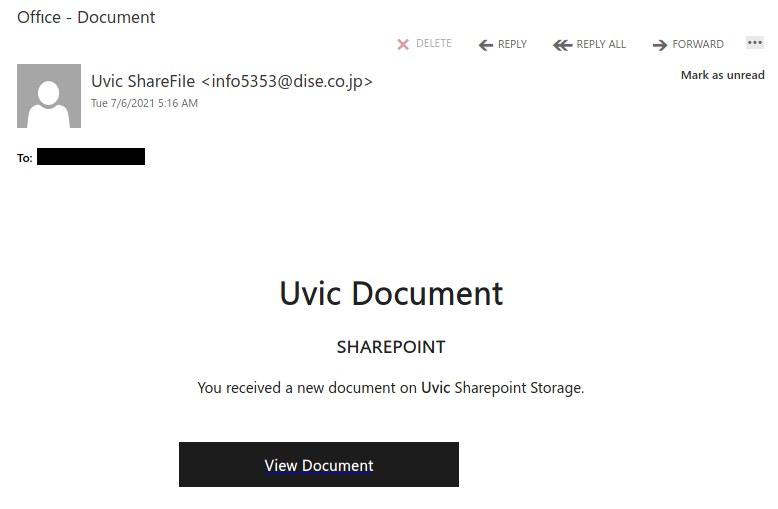
Another fake SharePoint email. The external email address is a giveaway but it may not be visible at first on a mobile email client.
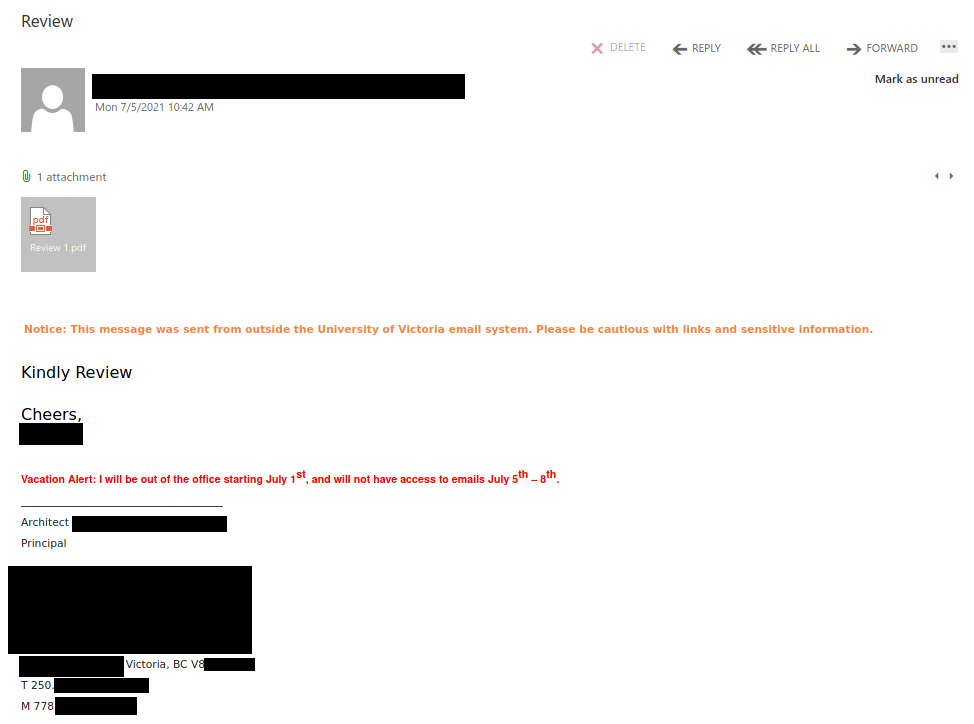
Recently there have been cases where a user at some other Victoria-area organization had their account compromised and used to send phishing emails. These emails come with a PDF attachment that poses as a M365 SharePoint file sharing notification and directs you to click on a link to login and view the shared file. That link takes you to a fake M365 login page to try and trick you into providing your username and password. If you opened this PDF, please reach out to your department’s IT support staff or the Computer Help Desk immediately.
If a phisher manages to compromise an account belonging to someone you know or have prior dealings with, they may try to take advantage of that existing relationship in their phishing attempt, hoping that you’ll think the message is safe and click on links or attachments. When in doubt, contact the sender via another communication channel that you know is trustworthy (e.g.: a known good phone number) to verify that the email is legitimate.
See also: CISO Blog post – How can I tell it’s really you?
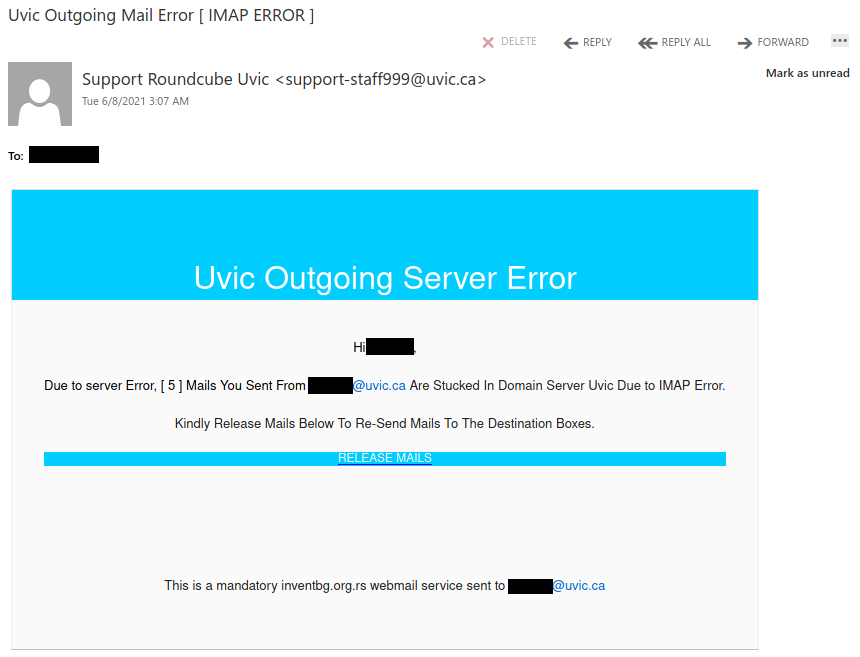
Sometimes organizations ‘quarantine’ email messages that might be suspicious, allowing the end user to review before releasing them to the user’s mailbox. This phish tries to fool the user into thinking they have messages that need to be released from that quarantine.
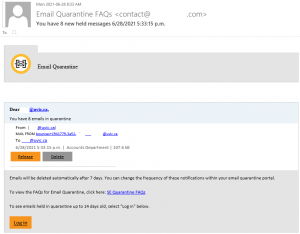
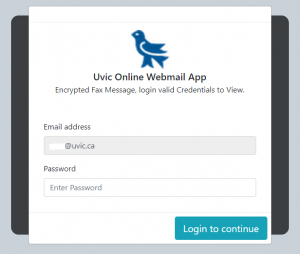
In this case, the fake login page was hosted on the Google Firebase storage service. The attacker used the UVic martlet image to try to fool users into thinking this is a legitimate UVic service, which it’s not.
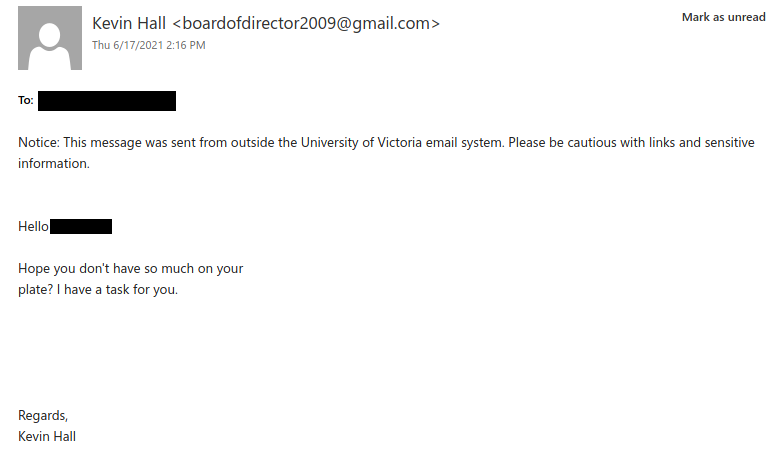
Gift card scammers often start by sending emails like the example below. They pretend to be a person in a position of authority (the president in this case) and ask the recipient if they are free to help with an urgent task. People who reply will be asked to purchase several hundred dollars’ worth of gift cards out of their own pocket and then send pictures of them with the numbers revealed to the scammer. If you’re curious, this CISO Blog post has a detailed example of how the correspondence can pan out.
We’ve also seen variations where the scammer begins by asking the recipient to send their mobile phone number. This lets the scammer shift to communicating by SMS to try and avoid detection.
Tips to avoid falling for these gift card scams:
Note how the phisher used a spoofed sender to make this phish look like it originated from within UVic (of course, it actually didn’t).
This phish pretends to be from an internal UVic fax service. It used a sender display name of “Uvic” but actually came from an external email address, which of course is a red flag. Also note the green “sender has been verified” banner–that is a fake one added by the phisher.
The phish also came with an attachment called “Uvic statement.pdf”. Do not open it–the contents direct you to login to a phishing site. In general, opening such attachments is very risky since they could contain phishing content or malware. If you opened this attachment, contact your department’s IT support staff or the Computer Help Desk immediately. 
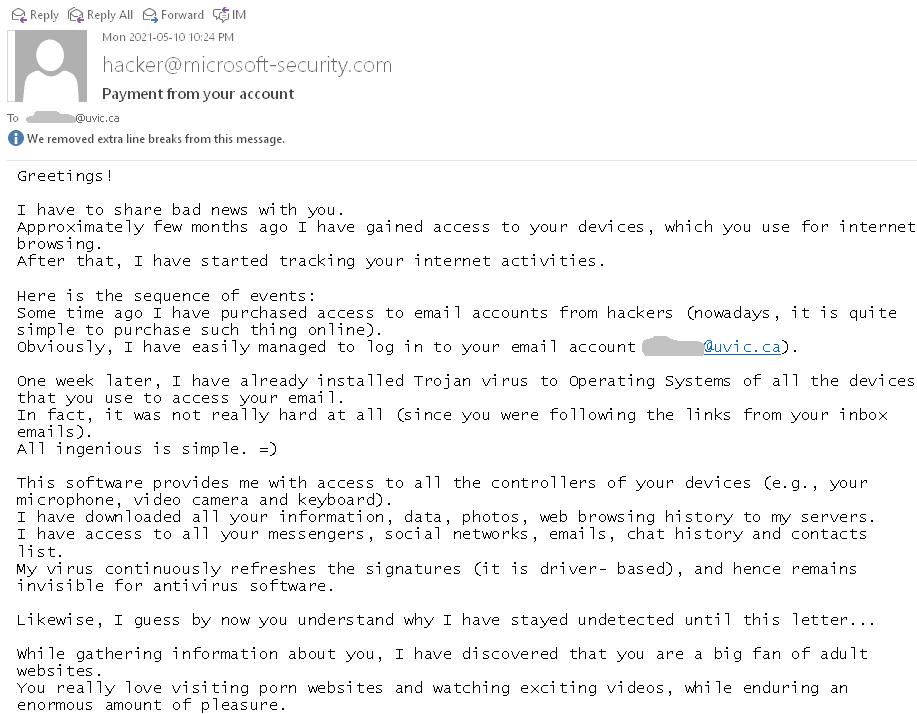
This type of scam is circulating again. See below a screenshot. Typically they are sent to a large number of email addresses retrieved after a certain breach. The scammer demands a payment in Bitcoin threatening to expose your secrets. In most cases they have only your email address and nothing else. In some rare cases they may list an old password (retrieved at some non-UVic breach) of yours in order to convince you. Do not re-use passwords. And of course do not answer those scams (even for fun!)
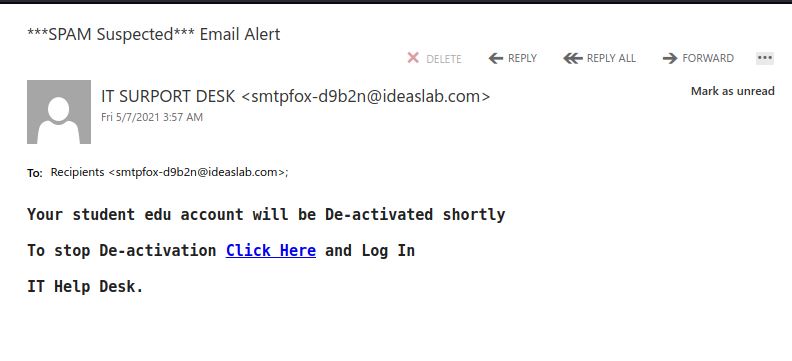
Subsequent to the Fake Microsoft logon this morning, urgent deactivation messages are suspect. We do not send out such messaging.
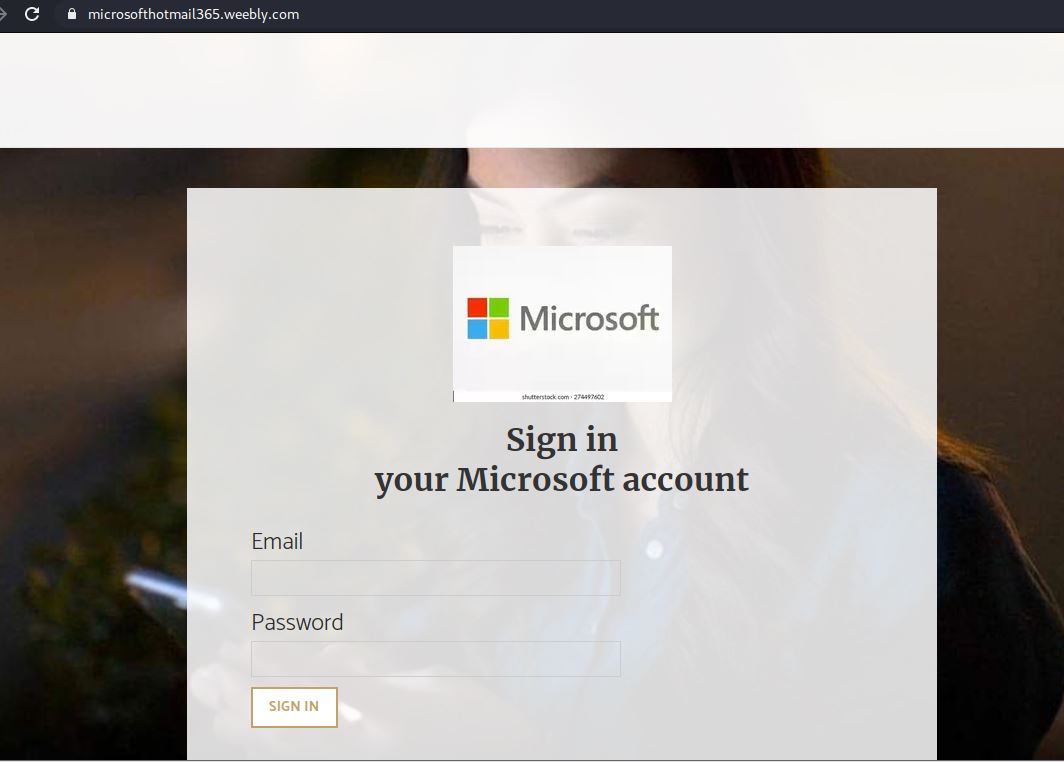
In this case the malicious or compromised Weebly site was already taken down.
Pause when you feel sense of urgency and when it doubt, simply contact the Computer Help Desk. We /Microsoft do not have extreme/urgent account disconnection notices or implementations or deadlines.
NOTE: Microsoft does not host their services on WordPress or Weebly. These and other free web hosting services are commonly abused/compromised for such phishing campaigns.
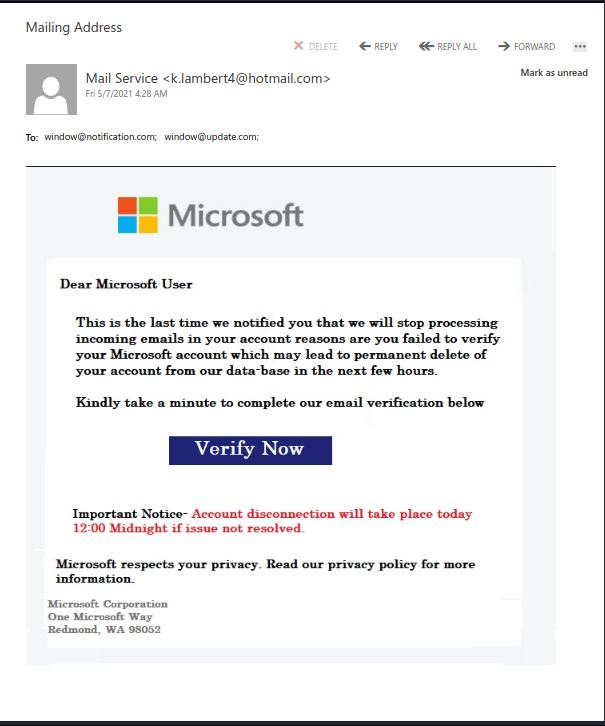
The Verify Now button will lead to a Fake Microsoft My Activation page hosted on a compromised WordPress site.
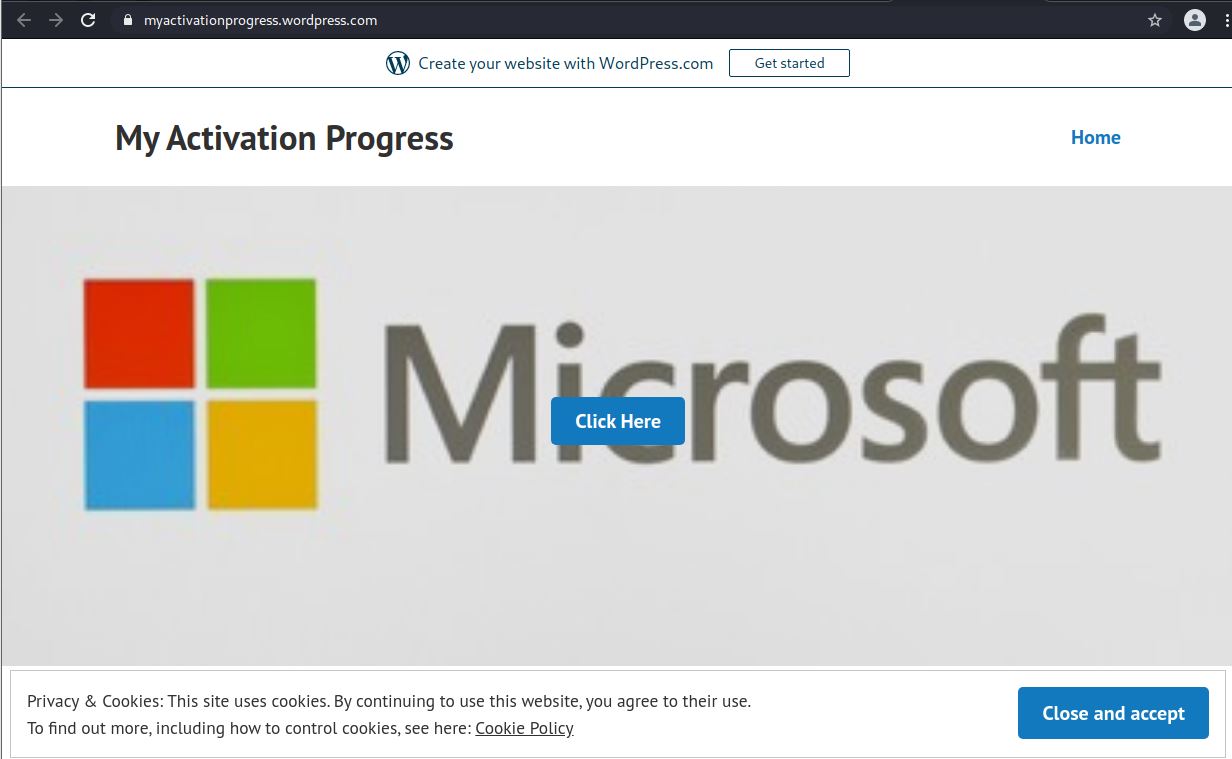
The Click Here button will land you on Fake Microsoft Logon page hosted on a compromised or malicious Weebly site.
Do not use buttons provided in a suspect page (eg. Close and accept button above). If you’d proceeded this far, simply close the whole browser instead and inform your IT Support contact.
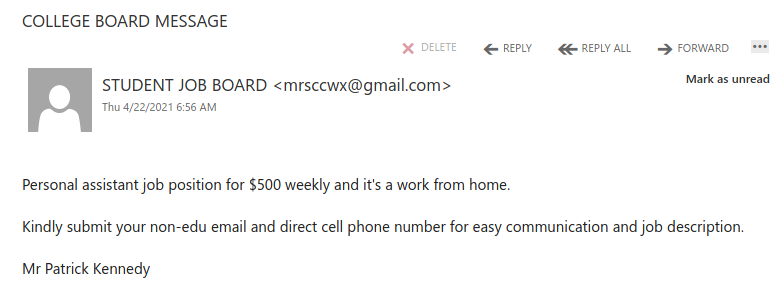
Work from home job scams are unfortunately very common right now with scammers trying to take advantage of people having financial difficulties due to the pandemic. If you receive an unsolicited email like this, do not reply with your email address, phone number or any other personal information. If you did, be extra vigilant about scams, phishing, smishing (SMS phishing) and vishing (voice phishing) since the scammers may view you as a promising target.
More on work from home job scams:
CBC News – Online job scams on the rise during pandemic year, fraud prevention expert says
CTV News – Better Business Bureau warning about these work-at-home scams
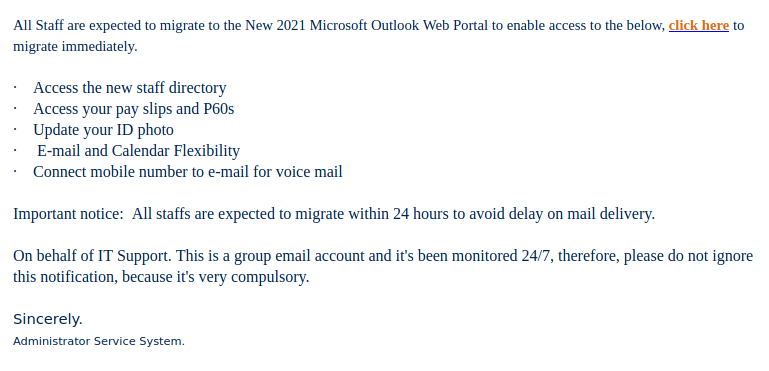
Various groups at UVic received this targeted phish. Note how the phisher used a spoofed sender to make the message look more legitimate. The URL that you can see in the phish message looks OK, but if you were to hover over those links you would find that they actually go to a phishing site on a completely different domain. This is why it is very important to hover over links to check the true destination before clicking on them.