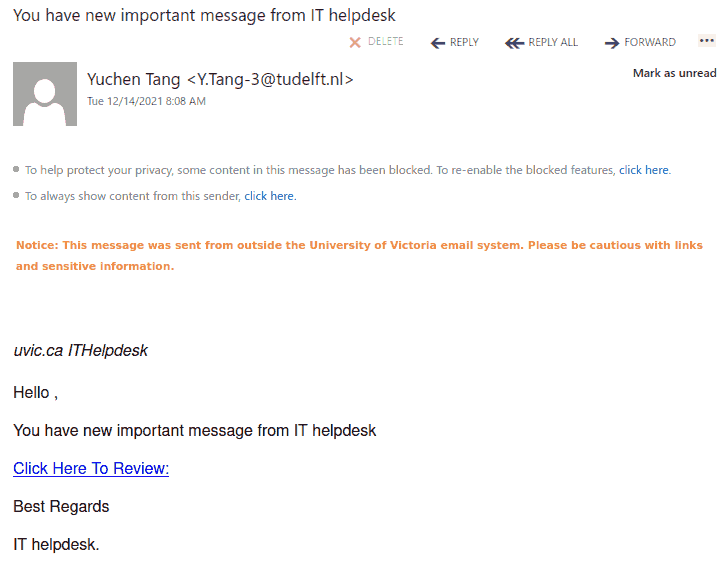
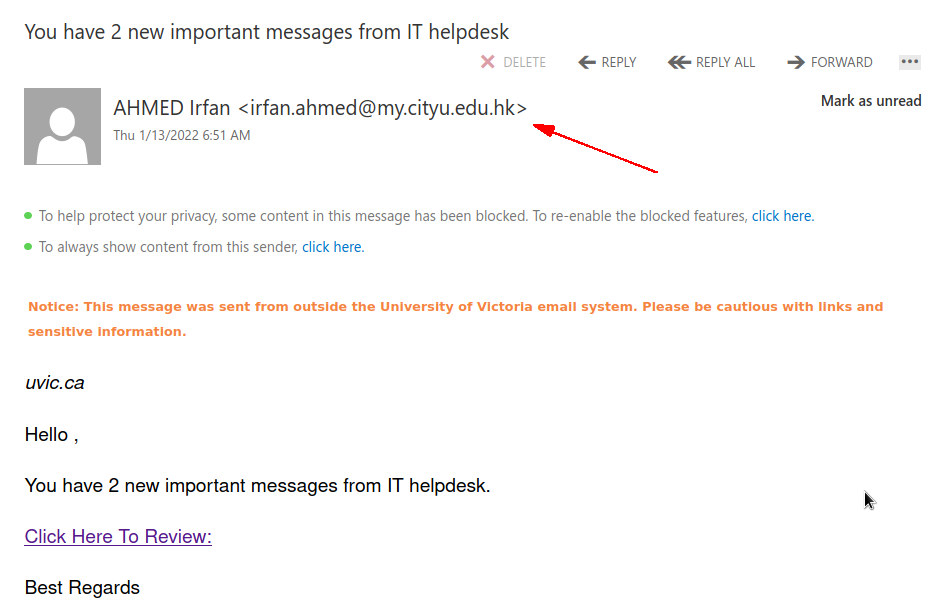
Many UVic users received a phish with this subject today. The text of the email looks quite trivial (see a screenshot below) but it leads to a very well copied fake UVic login page (also shown below). Another variation leads to a fake VPN login page. Note the address of the sender is external. Also it is easy to spot the links are external if you hover with the mouse cursor on those. Please do not click on them, do not be curious. Your computer may get malware even just by visiting such pages. Our experts investigate them by using specially isolated computers.
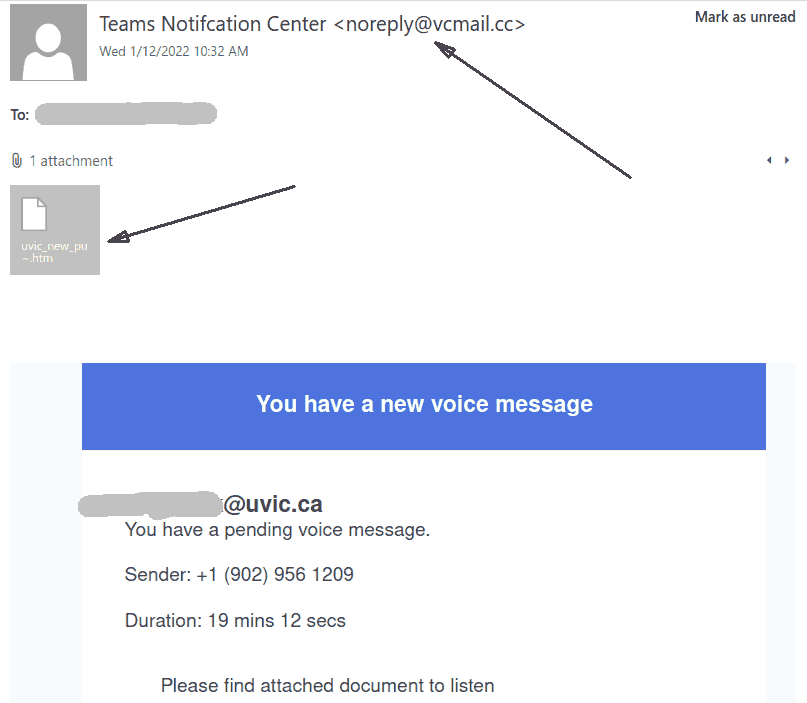
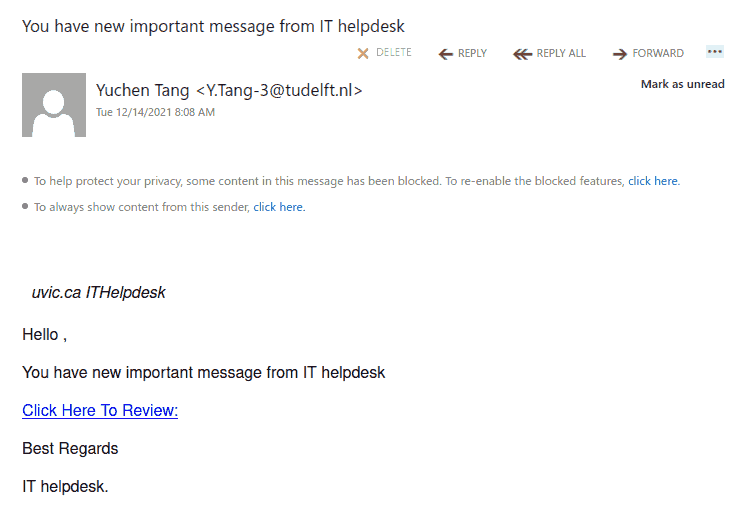
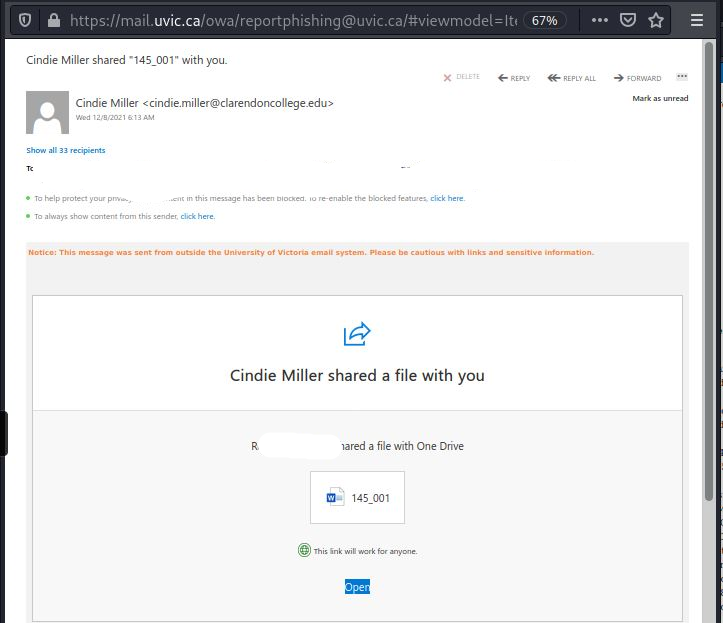
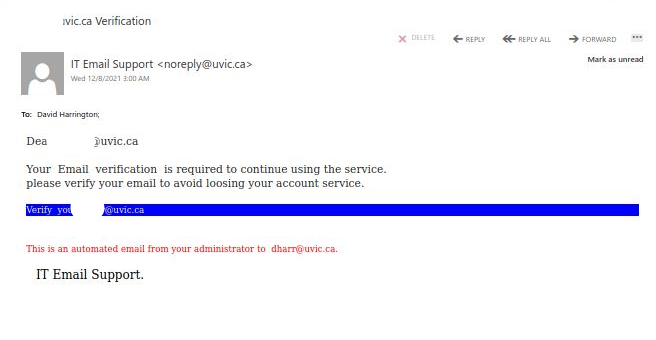
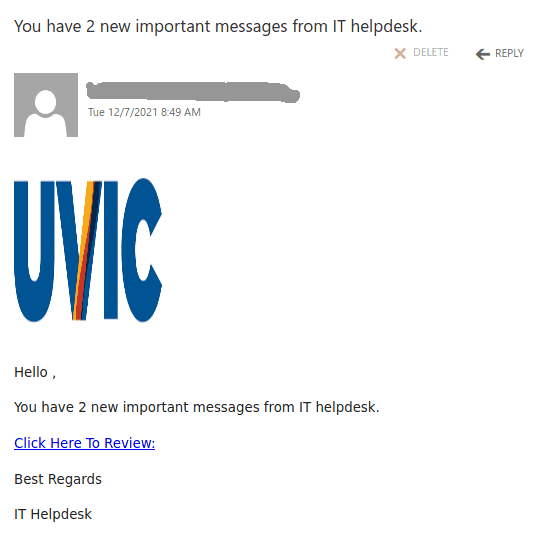
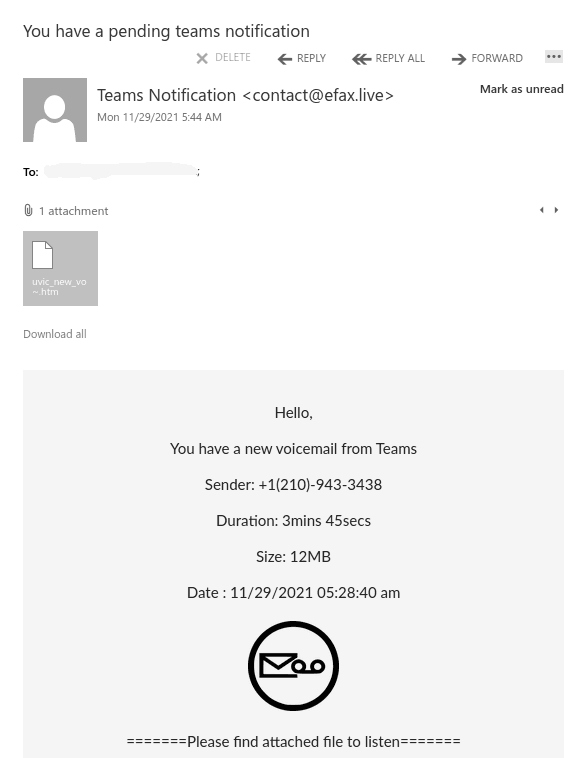
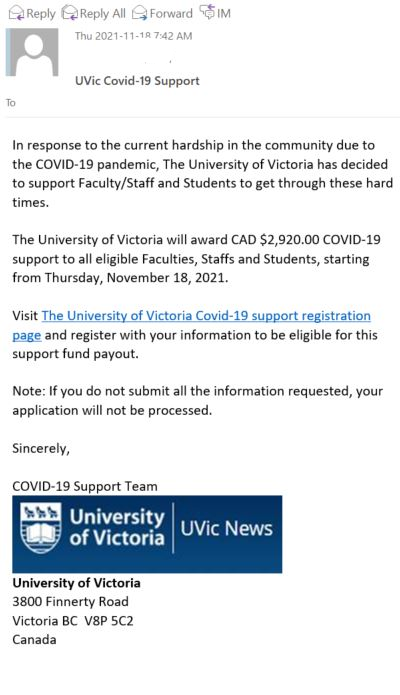
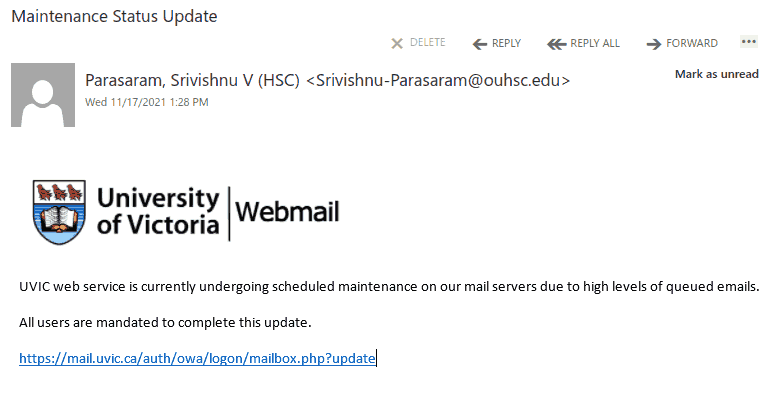
The email:
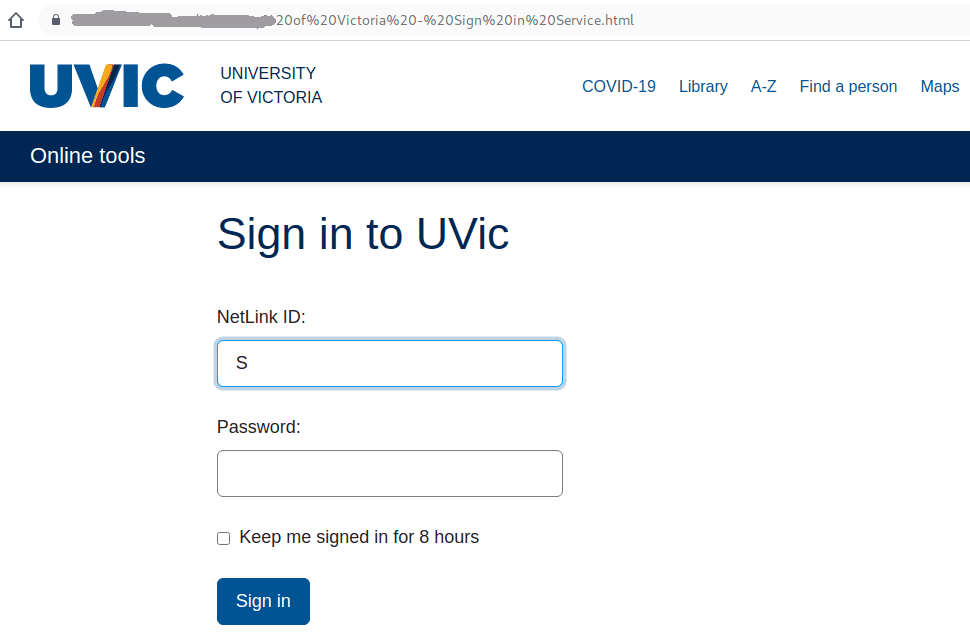
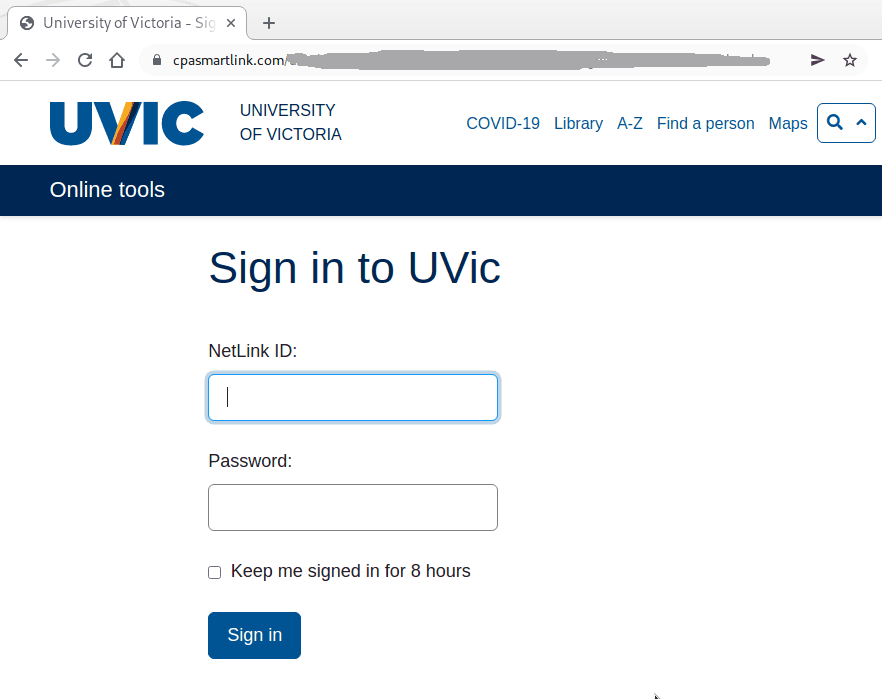
The fake login page:
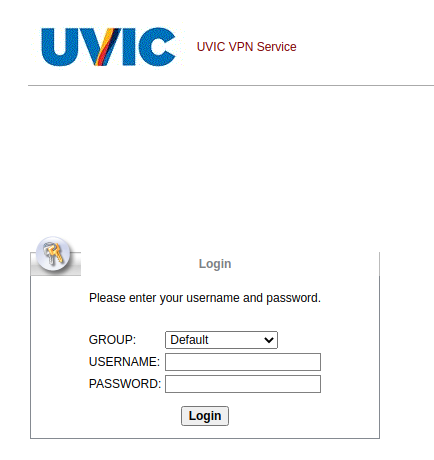
The fake VPN login page: