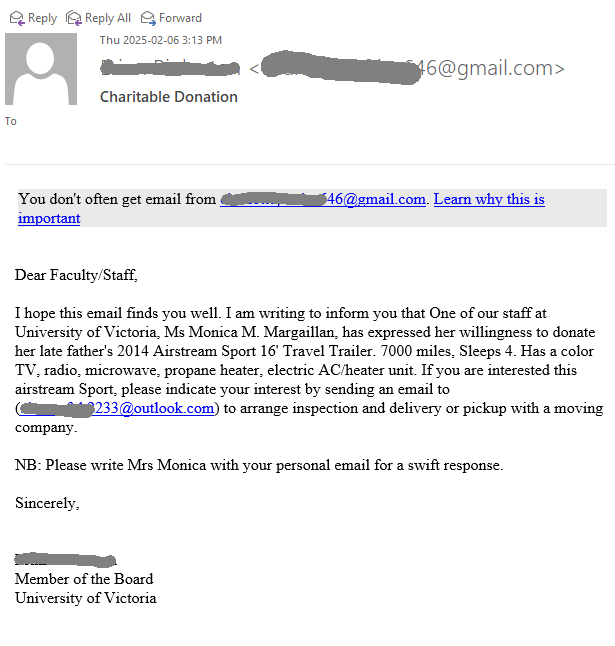
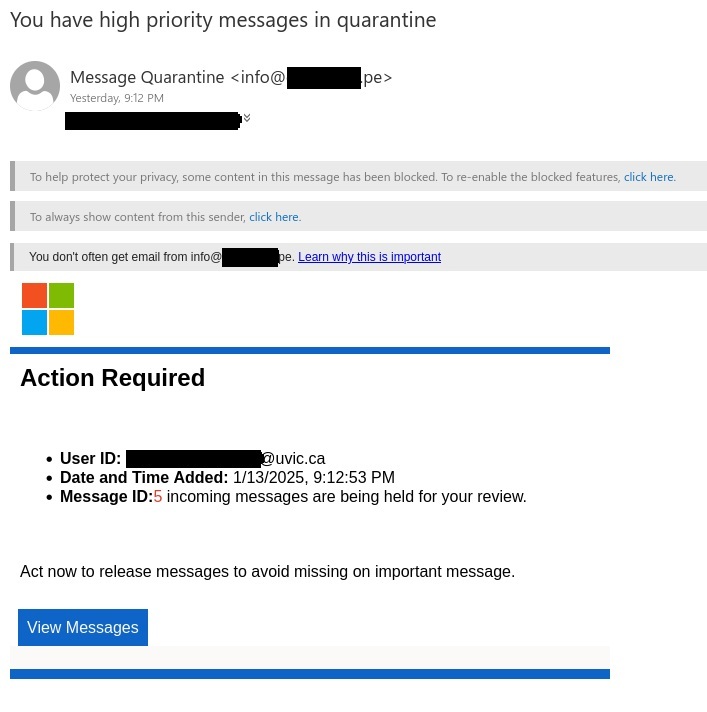
This email claims to be a document signing request from UVic. However, the sender (not shown here) was a long, partially randomized address from outside of UVic, which is the first red flag. The grammatical errors (especially the lowercase “victoria”) and the copyright footer’s erroneous reference to “University of victoria Corporation” are further signs that this email wasn’t actually from UVic. Hovering over the link will also reveal that its destination is not UVic or one of the cloud services that UVic has approved for university business.
Always look carefully at the email before you click on anything. Generally speaking, if the email doesn’t look quite right, it probably is a phish.

Signature-Required:University of victoria Resolution Document Completion Notice
Hi [redacted],
University of victoria Completed Document has been assigned to you for timely review and completion report.
File Name: University of victoria_Q4Remittance/Submission.pdf
Assigned To: [redacted]@uvic.ca
Open Document [link in big blue box]
Please take a moment to review this document for University of victoria.
Explore more with University of victoria
© Copyright University of victoria Corporation 2025.