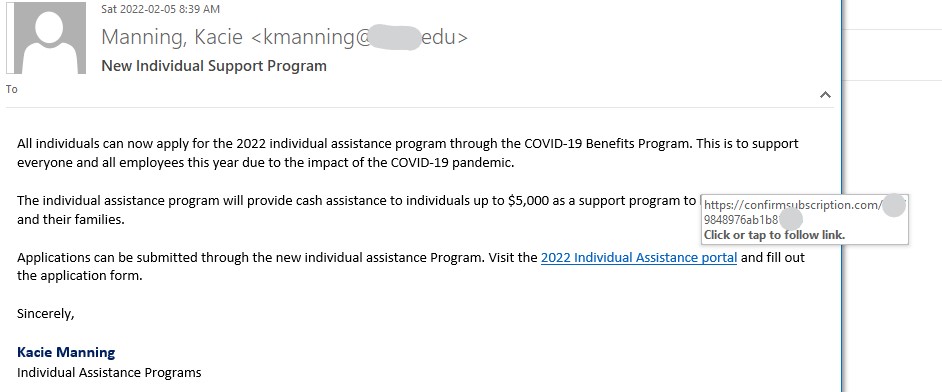
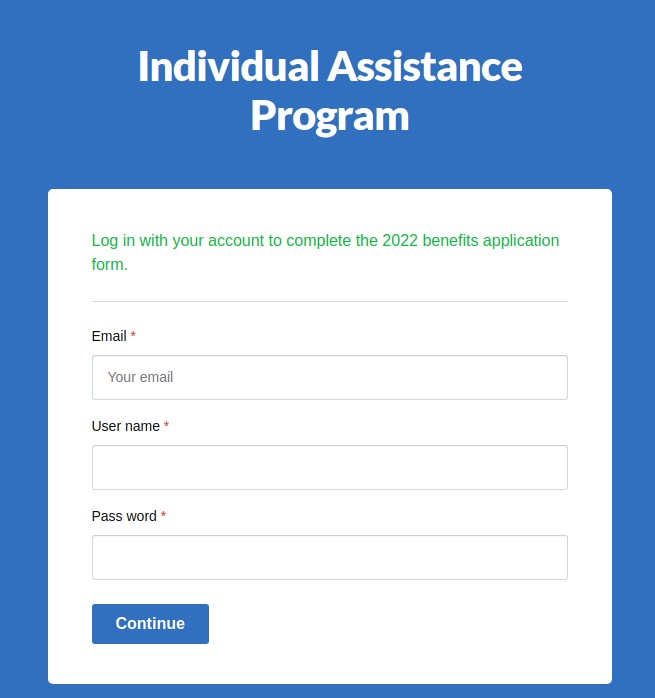
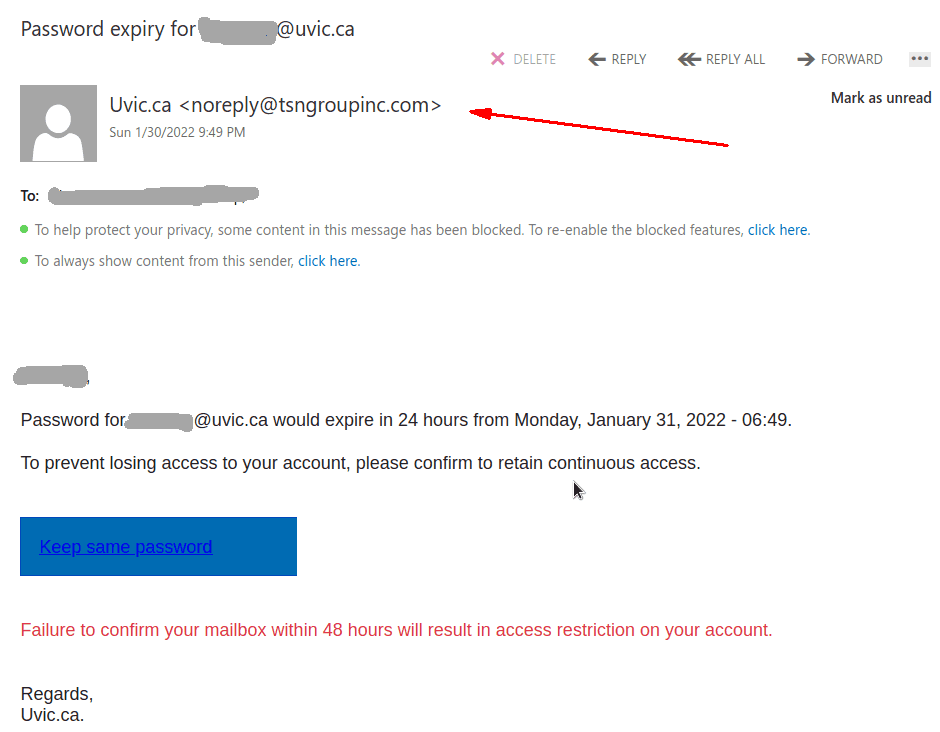
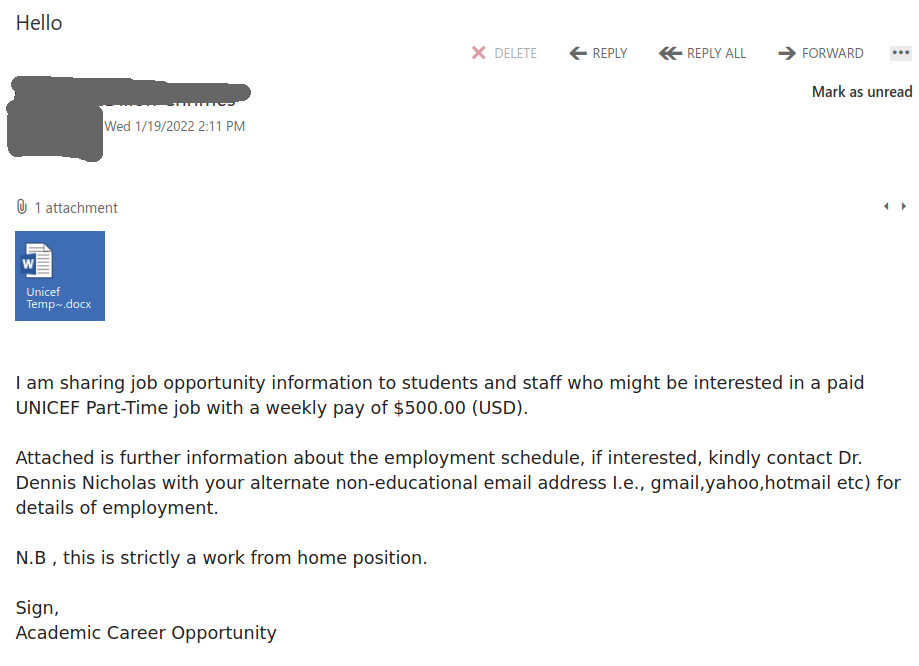
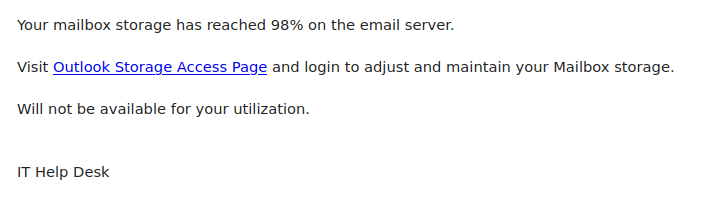
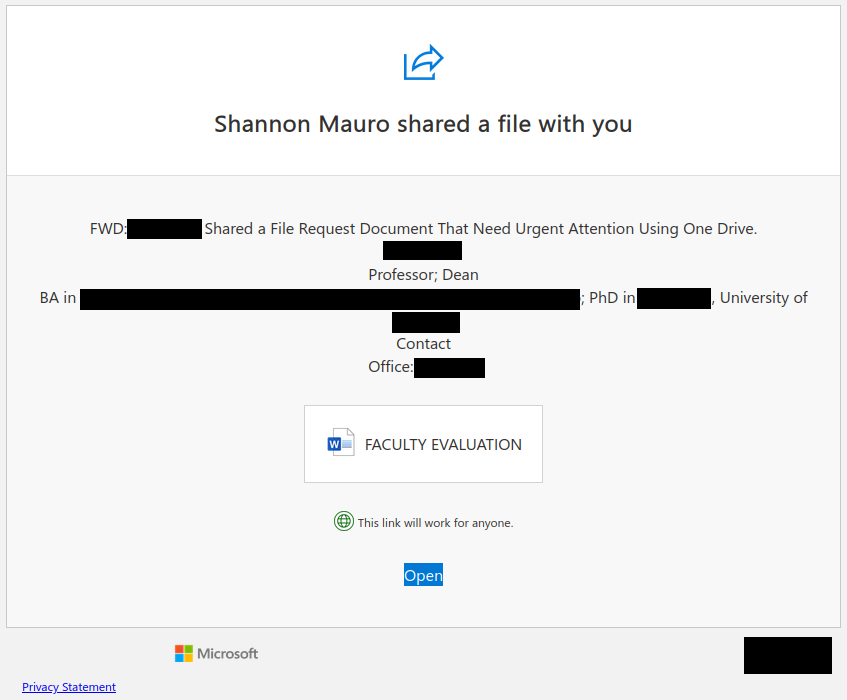
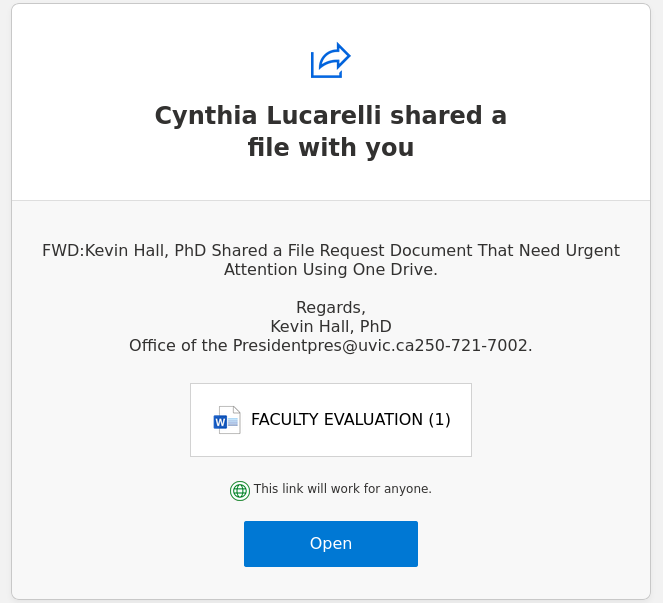
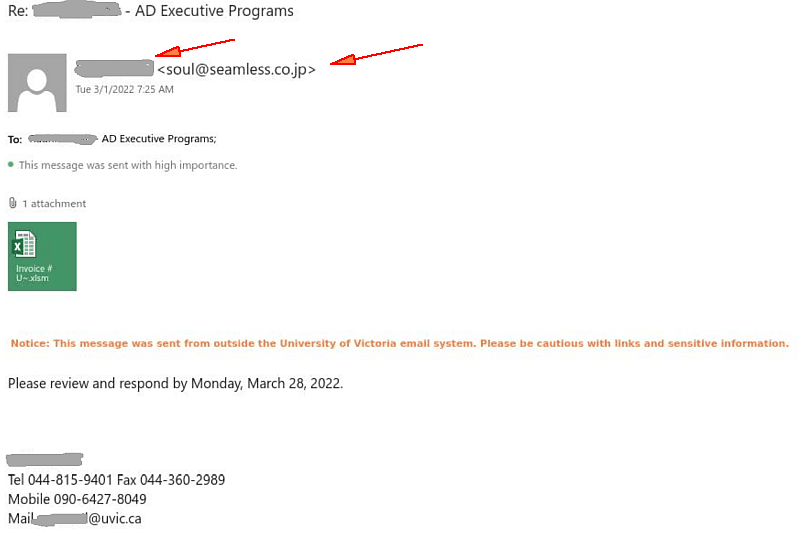
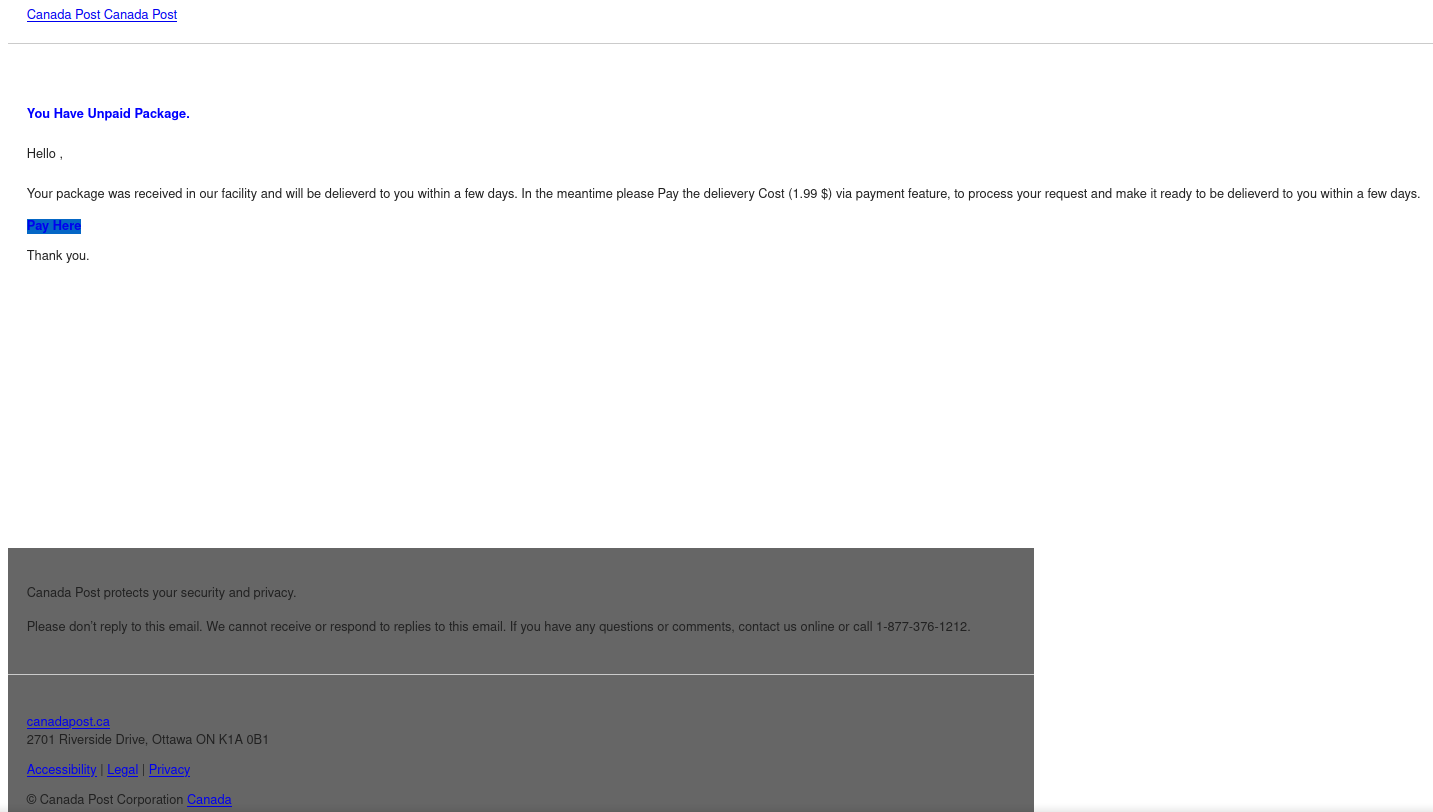
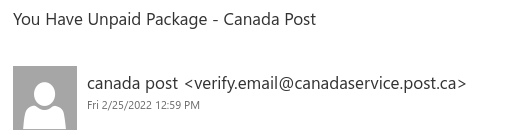
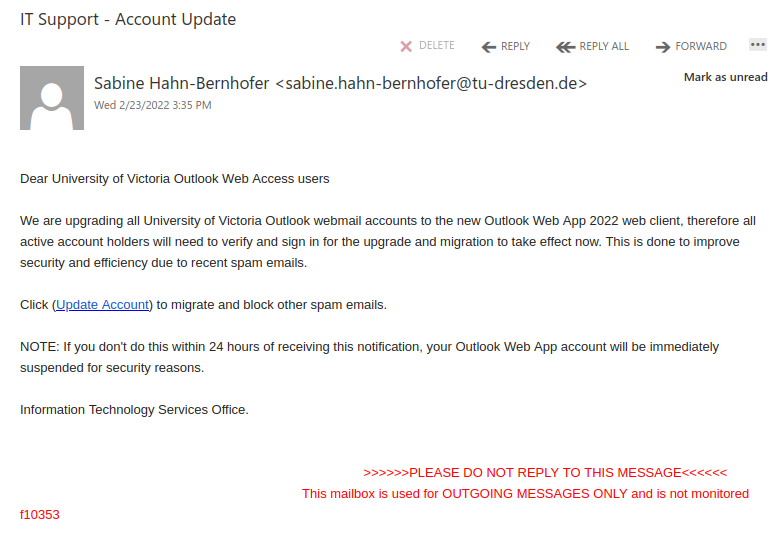
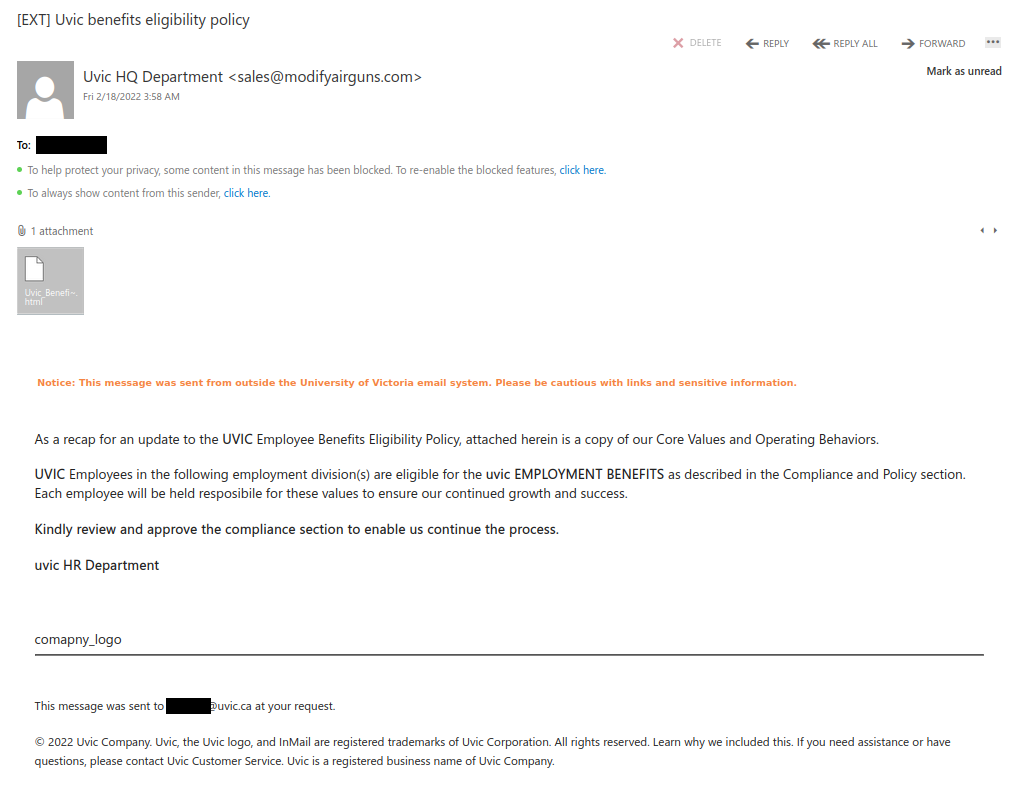
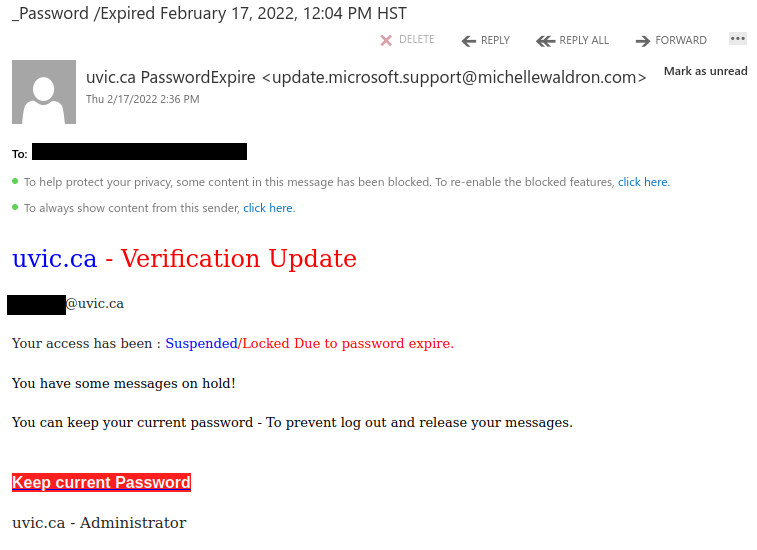
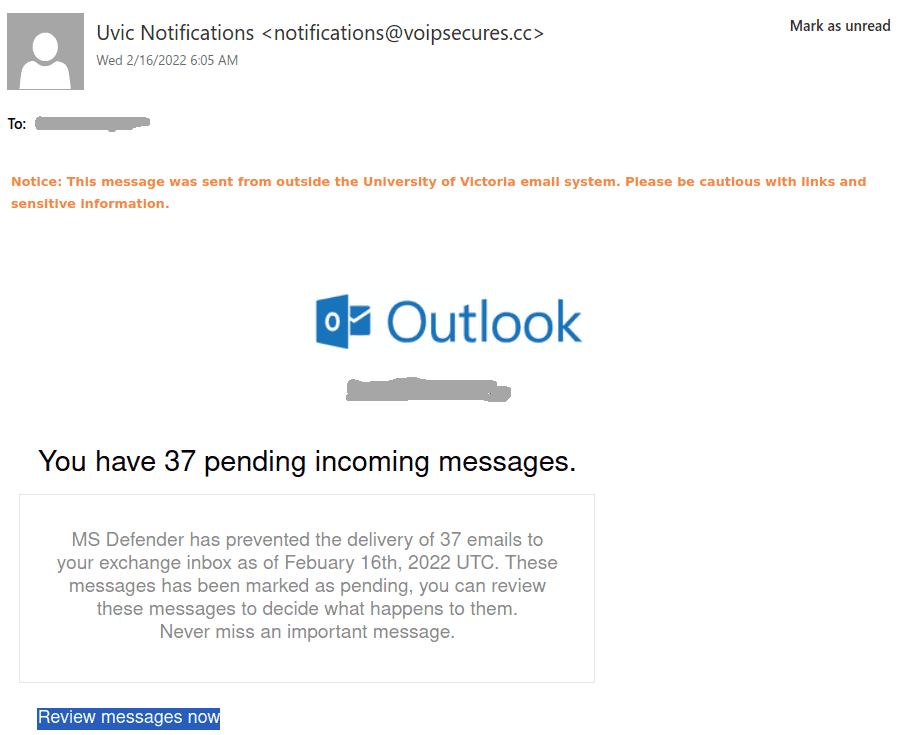
Today UVic users are attacked by emails containing infected Excel attachments. In some cases those impersonate UVic people and send to their colleagues (names redacted). In some cases the display name of the sender is just “uvic”. The sender address is clearly external. Note also their 044 phone numbers.
It can pretend to be an invoice or anything else as well.
Do not open these attachments!
Report by the phish button or call your desktop support for assistance.

 ——————————————————————————–
——————————————————————————– ———————————————
———————————————