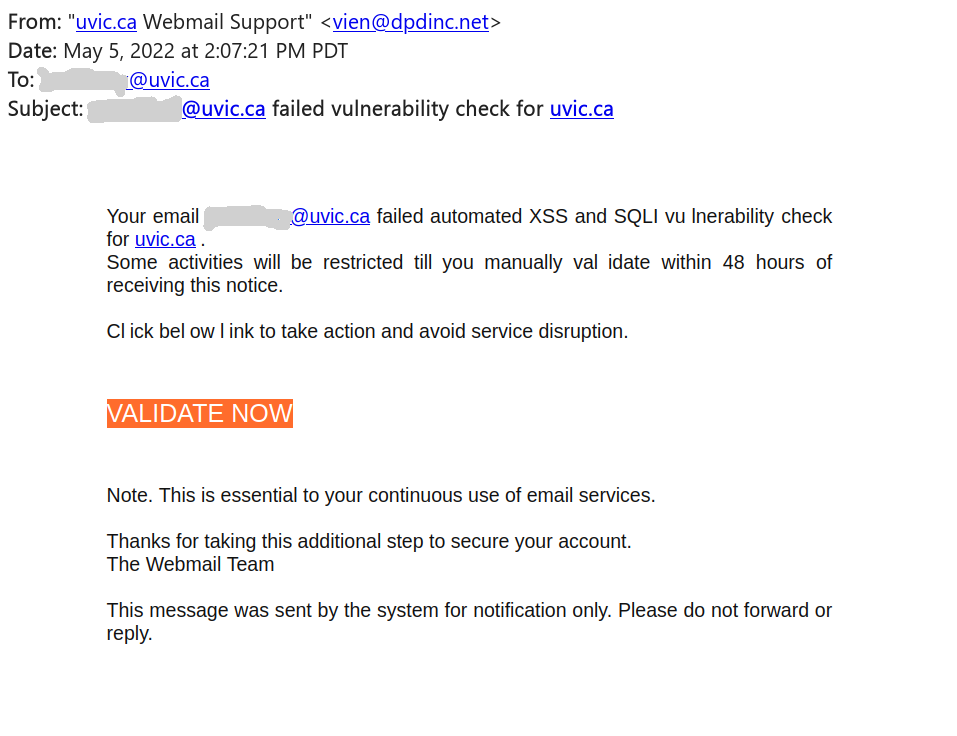
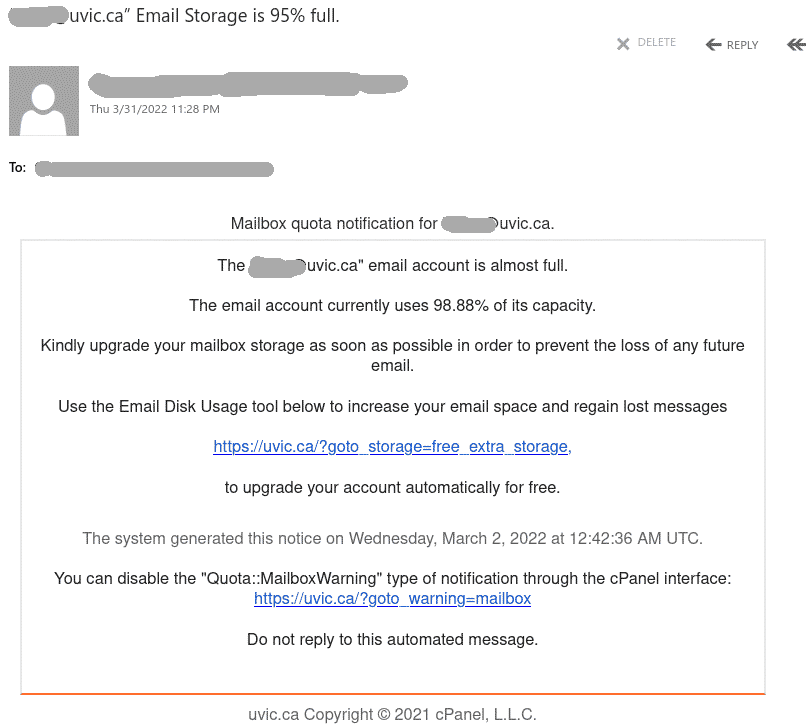
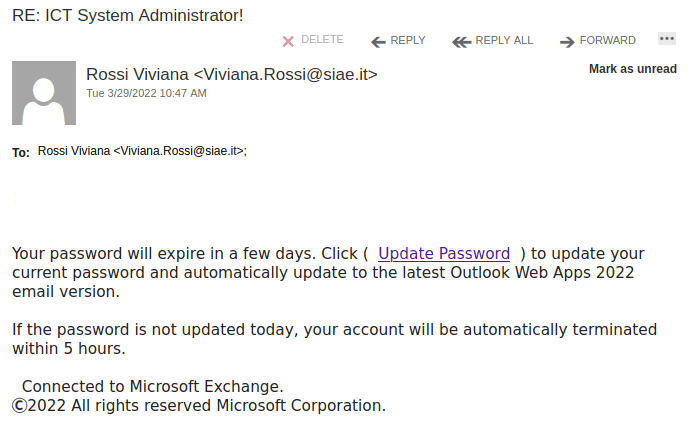
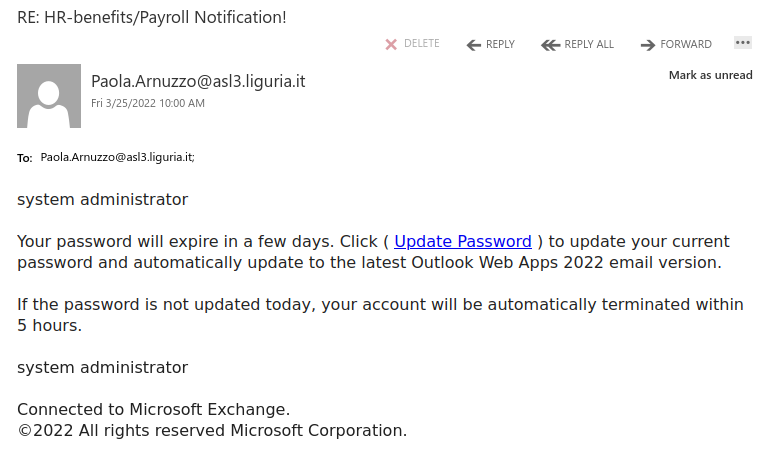
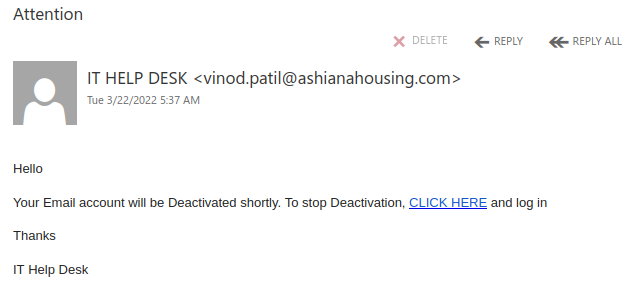
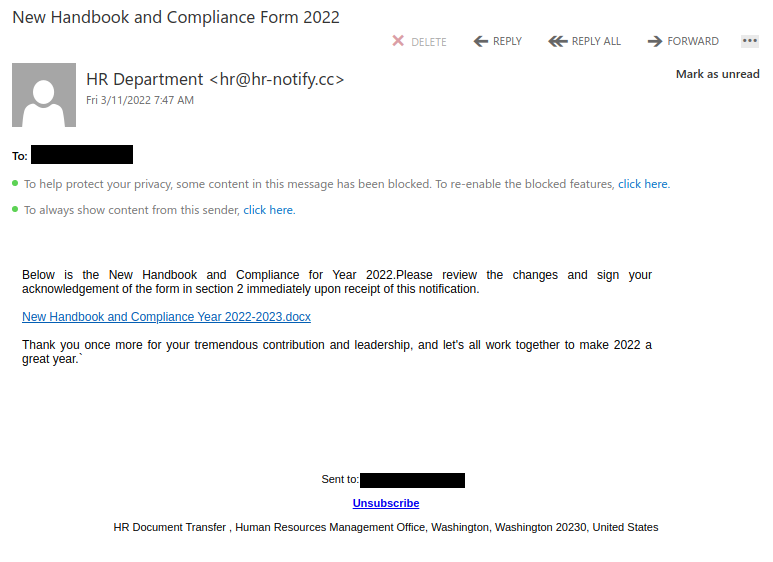
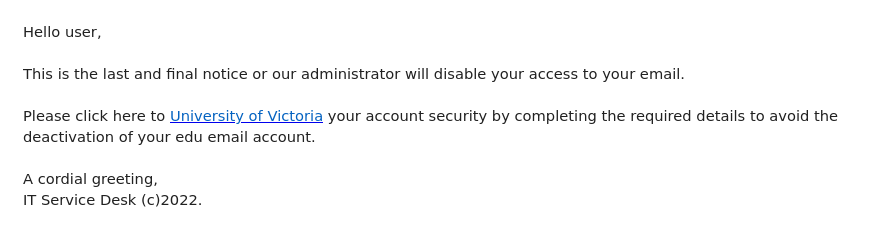
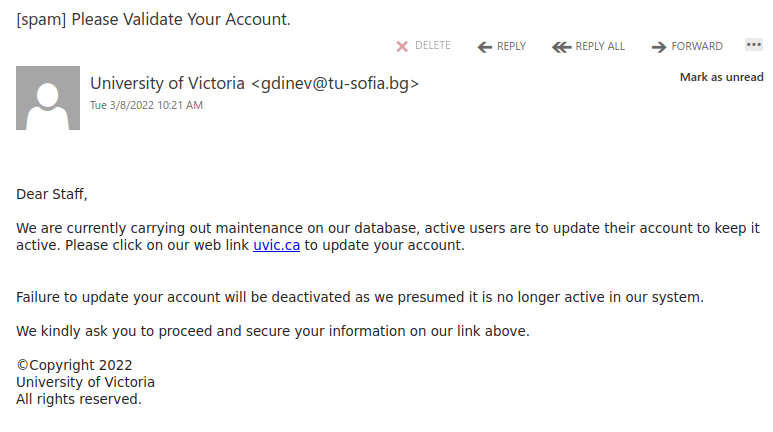
This phish is circulating around today. See a screenshot below.
Of course something must be wrong and of course you have to act fast. The sender pretends to be a “uvic webmail support” but clearly is using some external address. Note how the malicious actor deliberately put space in some words in the message body in order to evade automatic detection of phish, e.g. in the words “vulnerability”, “click”, “below”, “validate”
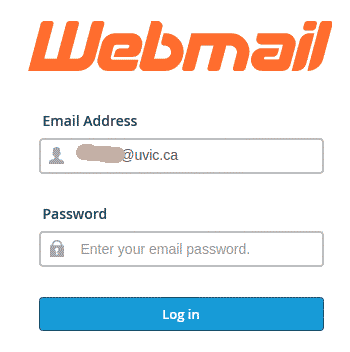
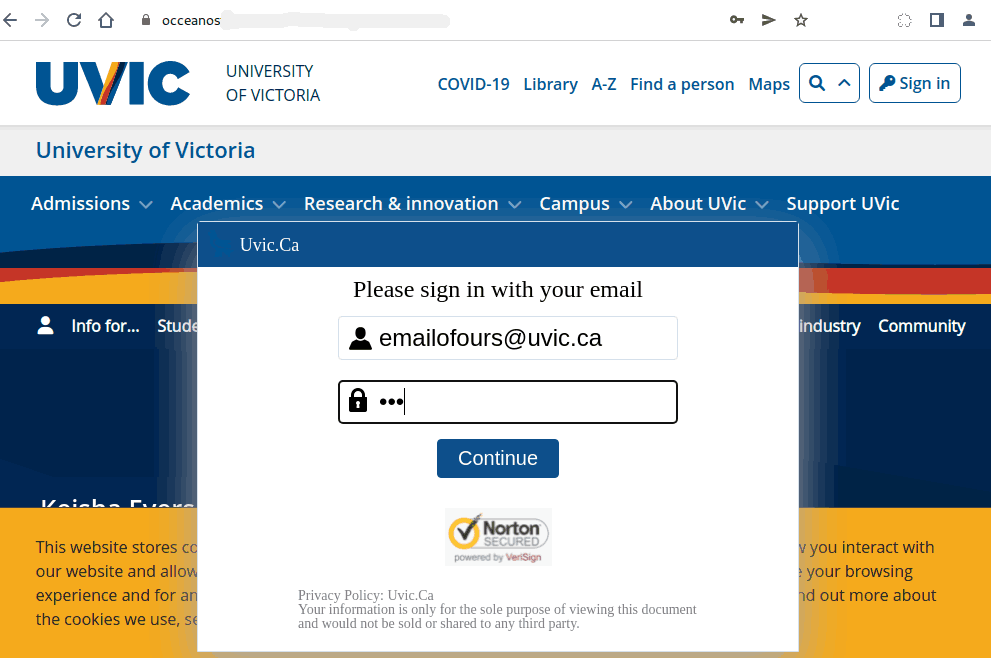
The link is external of course, and points to a fake roundcube mail page that’s created to steal your credentials.
Please never click on suspicious links, don’t be curious. Sometimes these pages may contain malware to infect your machine instantly. Our experts open these in a dedicated isolated environment.